Create a SAML IdP Connector
The SAML IdP connector allows SigningHub to connect with an external SAML v2.0 Identity Provider (IdP) to authenticate users both at the time of login and at the time of signing. There are two pre-requisites of configuring a SAML IdP connector which are:
- The IdP connector is used to get the metadata XML file from the third party i.e. SAML IdP provider (for which this connector is being created). It includes the IdP signing certificate, which is used by SigningHub to verify assertions. If it is not, this must be supplied separately along with the metadata.
- The SigningHub Service Provider requests signing key and associated certificate, e.g. PFX file, generated by using ADSS Server.
Create a SAML IdP connector
- Click the "Configurations" option from the left menu.
- Click the "Connectors" option.
The "Connectors" screen will appear. - Click
 from the grid header.
from the grid header.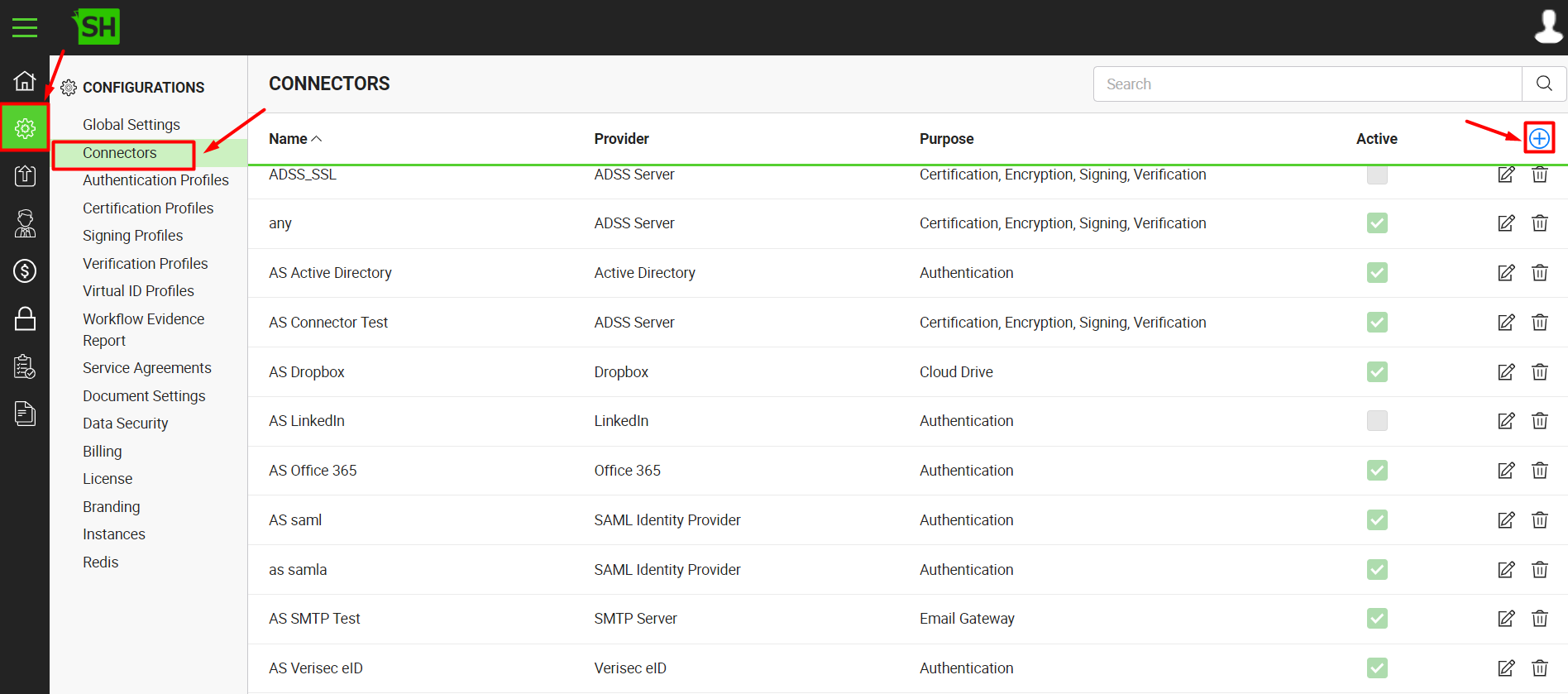
- A dialog will appear to add the connector details. The connector dialog is comprised of two screens, i.e. Basic Information and Details. Specify the basic information and click the "Next" button to provide the respective connector details.
- Click the "Finish" button. A new connector will be saved and displayed in the list.
See the below table for fields description.
|
SAML IDP Connector |
|
|
Fields |
Description |
|
Name |
Specify a unique name for this connector, such as 'My SAML IDP'. This connector will be used in the configuration of Authentication Profiles. |
|
Provider |
Select the provider for this connector, i.e. "SAML Identity Provider". |
|
Purpose |
This field will display the purpose of the selected provider above, i.e. the purpose of "SAML Identity Provider" is "Authentication. |
|
Logo |
Select an appropriate image in the jpeg, jpg, gif or png format for the connector's logo that will be displayed on the login screen. |
|
Browse IdP Metadata |
Browse the IdP metadata XML (from your machine) that is generated from the IdP server. This will auto fill in the related URLs in the below fields. You can also manually specify each URL on individual basis. |
|
HTTP POST login URL |
HTTP POST login URL that is populated from the IdP metadata XML. |
|
HTTP POST Logout URL |
HTTP POST logout URL that is populated from the IdP metadata XML. |
|
HTTP Redirect Login URL |
HTTP redirect login URL that is populated from the IdP metadata XML. |
|
HTTP Redirect Logout URL |
HTTP redirect logout URL that is populated from the IdP metadata XML. |
|
Binding Type |
This will specify the SAML request type, i.e. Post or Redirect. By default the "Redirect" option is selected. |
|
Signature Algorithm |
This will specify the signature algorithm of IdP server, i.e. SHA1 or SHA256. By default the "SHA1" option is selected. |
|
IDP Signing Certificate |
As the name indicates this Identity Provider (IDP) Signing Certificate will be used to verify signed response send by IDP. |
|
SP Request Signing Certificate (PKCS#12) |
Browse and select a request signing certificate (PFX file) for the service provider (SP). This certificate (PKCS#12) will be used to perform signature for request. |
|
SP Request Signing Certificate Password |
This will specify the password of the SP Request Signing Certificate (PKCS#12). |
|
Required Signed Assertions |
Enabling this check box will allow the SP to verify the signature of the signed response send by IdP. IdP signing certificate will be used for this verification. |
|
Authentication Request Signed |
This check box will enable the user to authenticate requests signing preferences, when it will be enabled, then the SP (service provider) will be able to send signed request to IdP using the SP Request Signing Certificate (PKCS#12) to sign the request. |
|
Export SP Metadata |
Click it to download a signed "SPMetaData.XML" file on your machine for the IdP server. Update this XML on the IdP server for the client-end configuration. |
|
Active |
Click this check box to make this connector active. Inactive connectors cannot be configured in the Authentication Profiles. |
|
|
IMPORTANT LINKS
|
|
|
It is recommended that the email address must be in the 'mail', 'email' or 'E-Mail Address' format while configuring outgoing claim types attribute mapping for a relying party. |
See Also
- Create a LinkedIn Connector
- Create a Google Connector
- Create a OneDrive Connector
- Create an ADSS Server Connector
- Create a Clickatell Connector
- Create a Twilio Connector
- Create a Worldpay Connector
- Create a Stripe Connector
- Create an SMTP Server Connector
- Create an Active Directory Connector
- Create a Dropbox Connector
- Create a Salesforce Connector
- Create a Google Drive Connector
- Create a HubSpot Connector
- Create an Office 365 Connector
- Create an ADFS Connector
- Create a Maxmind GeoIP Connector
- Create a Firebase Connector
- Create a Freja Mobile Connector
- Create a Freja eID Connector
- Create an Azure Blob Connector
- Create an Azure Active Directory Connector
- Create a Bank ID Connector
- Create a Captcha Connector
- Create an SMS Connector
- Create an itsme Connector
- Create a T1C Connector
- Create a File Scanning Connector
- Create a CSC Connector
- Create an OAuth2.0 Connector
- Create an OIDC Connector
- Edit a Connector
- Delete a Connector
- Search a Connector


