CRL Logs
The CRL log records all system events associated with the polling, retrieval and verification of CRLs for the registered CAs. The log records should be reviewed regularly to ensure CRL polling is being managed as expected.
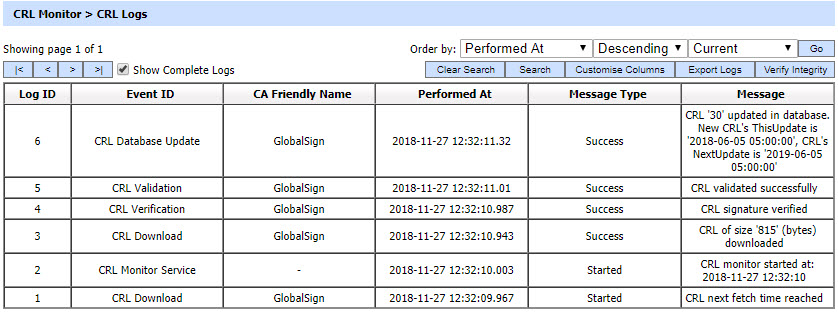
Each item in the screenshot is described below:
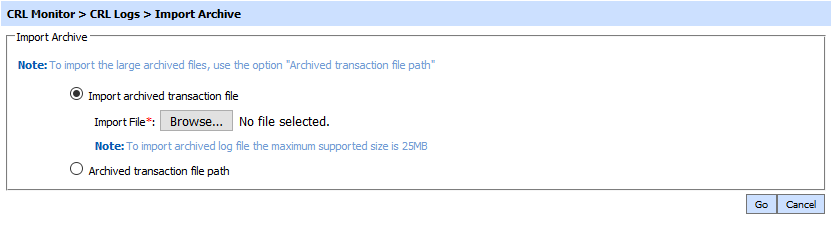
The CRL Monitor Service transaction records can be sorted in either ascending or descending order by selecting a table column from the drop down list. From the drop down menu in above screen, choose Import Archived and click on Go button. This will show the following screen:
| Item | Description |
| Import archived transaction file |
Use this option to browse the archived log file in zip format from the operator machine. By using this option the archived log file is uploaded on the ADSS Server. It can be an expensive operation if the file is of large size so the operator is allowed to upload a file with maximum size up to 25 MB. Use the archived file path option for files bigger than 25 MB. |
| Archived transaction file path |
Use this option if the file size is greater than 25 MB. This option does not upload the archived file to the server. Rather the server reads the file from given file path before importing which is faster than the above option. You can either specify the local file system path or a network path. Note: Do specify the archived log file name in the file path. |
The archived files were created in the csv format till ADSS Server v4.7.5 but from v4.7.6 and onward the archived files are zipped to save the disk space when archiving. If you are importing the archived files created using a pre-v4.7.6 deployment to ADSS Server v4.7.6 or later then first zip them before importing otherwise ADSS Server will not recognise them as correct archived files.
As explained above, clicking on the Search button on CRL Monitor Transactions Log Viewer displays following screen:
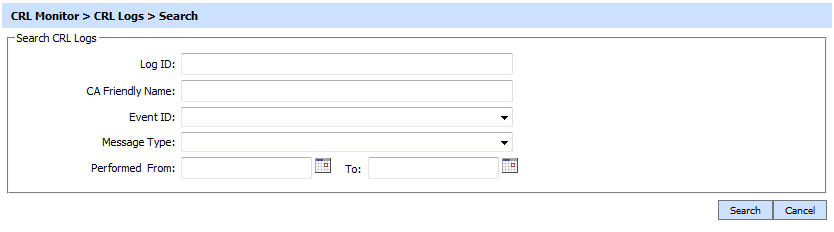
If "_" character is used in the search then it will act as wildcard.
Clicking on the Customise Columns button on Signing Transactions Log Viewer displays following screen:
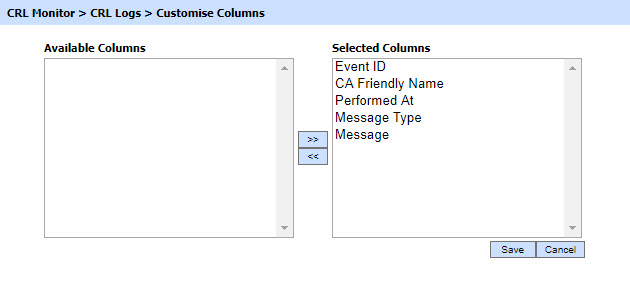
By default all columns are in the "Selected Columns" list. In order to hide a column move the required column to "Available Columns" list.
Each log record within the database is protected with a cryptographic HMAC checksum to detect any intentional or accidental modification of records. Clicking the Verify Integrity button verifies the log integrity by checking each checksum and generates a report as shown below:
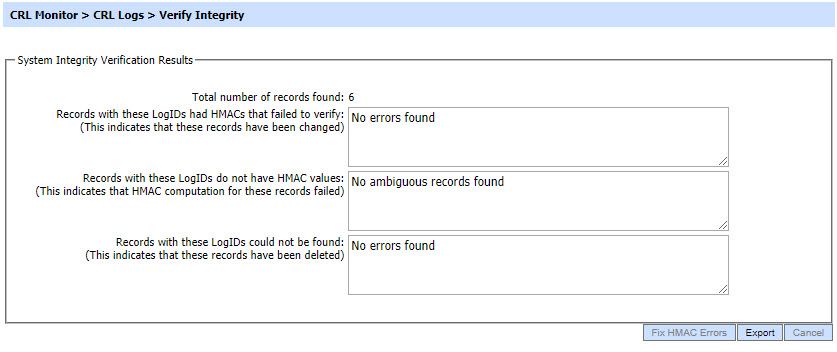
Click on the Export Logs button to export the request/response to a network file. Clicking the Fix HMAC Errors button will re-calculate the HMAC for tempered transaction logs records for this module.
Note: This option will not detect the unauthorized deleted records but it will only fix the unauthorized modifications and/or ambiguous records for which HMAC value is not present/incorrect.
The Verify Integrity feature is available for the transactions log of all services within ADSS Server.
See also