Transaction Logs
The OCSP Service Transaction Logs provides a record of each request made to the OCSP Service and each response returned by the service:
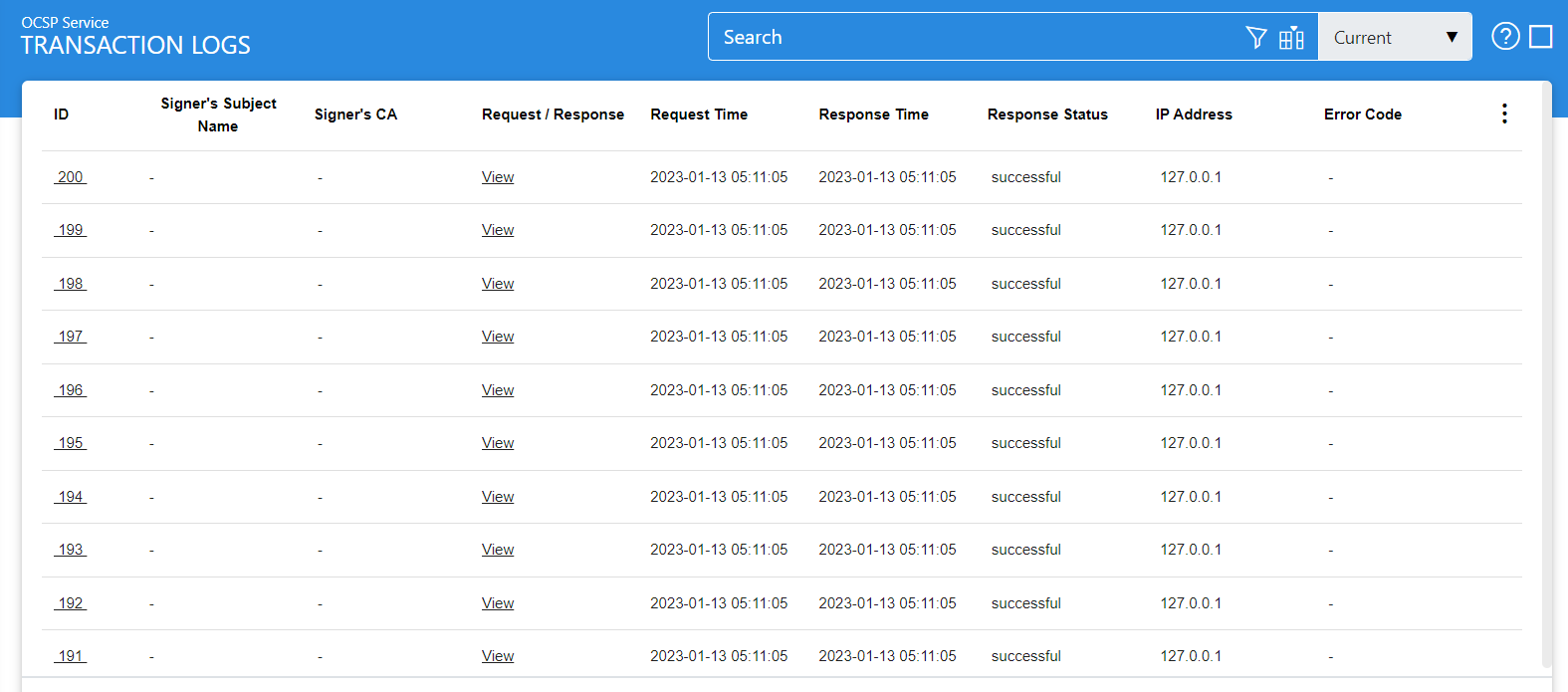
Each item in the above screenshot is described in the following table:
|
Items |
Description |
|
Clear Search |
After a Search this window will only show the filtered records. The Clear Search button is used to view the full set of records. |
|
Search |
This opens a new window where search criteria can be entered based on each column of the transaction grid. |
|
Customise Columns |
This opens a new window to configure which column need to be shown in the grid and which column need to be hidden. See below for more details. |
|
|< < > >| |
These buttons are for navigating the different pages of the transaction log. Note: The number of records shown per page is configurable from within Global Settings. |
|
Export Logs |
This button is used to export the selected transactions log into a zipped CSV file in which each column is separated by literal '~&~'. The file can be viewed using Microsoft Excel. However, in order to view and analyze the contents of the file in detail (all the archived transactions etc.), the user needs to import the file into ADSS using the Import Archived option. |
|
Verify Integrity |
Verifies the integrity of the signing service transaction log records. It detects tampered and deleted records and generates a report that can be exported to a physical drive. Note: When exporting HMAC verification reports, it is recommended to save the file with “.html” extension so that the report can be viewed in an internet browser. |
|
Show Archived |
This opens a new window where you can import and view previously archived file i.e. archived/exported transactions log. |
|
Log ID |
A unique serial number for the log record, it is system-defined and not part of the request/response messages. Having selected a particular transaction, this link shows the detail within the log as OCSP Service processes the request (see below). |
|
Signer's Subject Name |
This column specifies Distinguished Name (DN) of the relying party who sent the request. Note: This column is only filled in if the request was signed. |
|
Signer's CA |
This column identifies the CA that issued the Relying Party’s certificate. Note: This column is only filled in if the request was signed. |
|
Request/Response |
Provides a link to view the request/response messages. |
|
Request Time |
Records the date/time when the request was received. |
|
Response Time |
Records the date/time when the response was sent. |
|
Response Status |
This shows whether a “success” or “failure” response was returned. |
|
Total Cert IDs |
This column identifies total number of CertID contained in an OCSP request (i.e. the total number of certificates to be validated by the OCSP service). |
|
TLS Cert |
Clicking on “View” link under this column displays the TLS client authentication certificate. The “View” link is only present when TLS client authentication was used to send requests to the signing service. |
|
Signing Cert |
Clicking on “View” link under this column displays the request signing certificate. The “View” link is only present when a signed request was sent to the signing service. |
|
IP Address |
Records the IP address of the requester. |
|
Error Code |
Hover your mouse over the "View" link to show the error message e.g. Signature computation failure, Signing Service Disabled etc. |
|
|
After an OCSP transaction has been performed, it takes 10 seconds (approx.) to display the transaction details in the Transaction Log Viewer. |
The OCSP Service transaction records can be sorted in either ascending or descending order by selecting a table column from the drop down list. From the drop down menu in above screen, choose Import Archived and click on Go button. This will show the following screen:
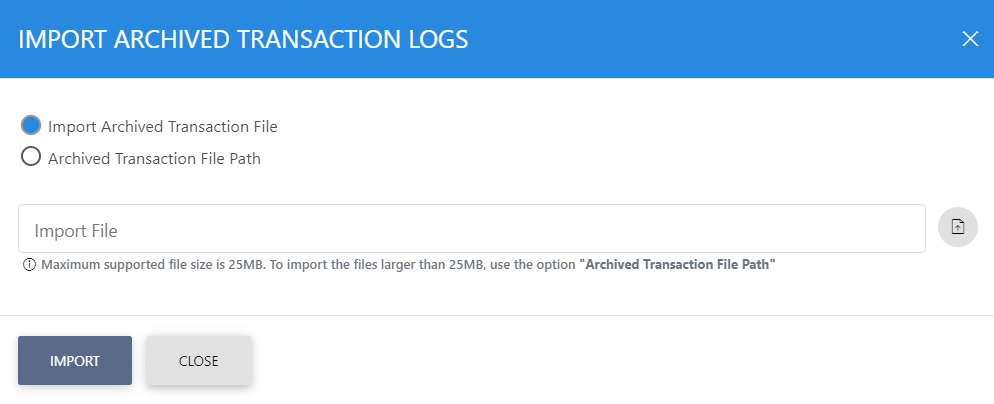
Each item in the screenshot is described below:
|
Items |
Description |
|
Import archived transaction file |
Use this option to browse the archived log file in zip format from the user machine. By using this option the archived log file is uploaded on the ADSS Server. It can be an expensive operation if the file is of large size so the user is allowed to upload a file with maximum size up to 25 MB. Use the archived file path option for files bigger than 25 MB. |
|
Archived transaction file path |
Use this option if the file size is greater than 25 MB. This option does not upload the archived file to the server. Rather the server reads the file from given file path before importing which is faster than the above option. You can either specify the local file system path or a network path. Note: Do specify the archived log file name in the file path. |
|
|
The archived files were created in the csv format till ADSS Server v4.7.5 but from v4.7.6 and onward the archived files are zipped to save the disk space when archiving. If you are importing the archived files created using a pre-v4.7.6 deployment to ADSS Server v4.7.6 or later then first zip them before importing otherwise ADSS Server will not recognise them as correct archived files. |
|
|
For importing OCSP Service archived logs follow these steps: Follow these instructions to add the main and details OCSP log files in a zip archive before importing.
If the above order is not followed then archive import will be failed for the OCSP Service. |
As explained above, clicking on the Advance Search icon on OCSP Transactions Logs displays following screen:
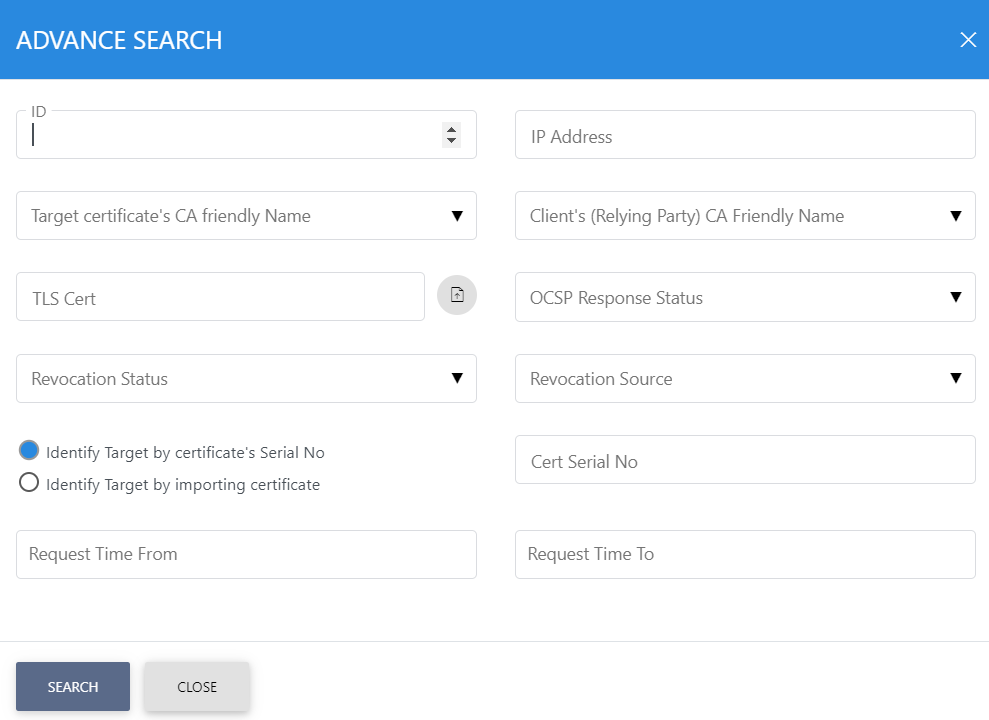
This helps to locate a particular type of OCSP service transaction. The transaction can be searched based on "Log ID", "IP Address", "Target certificate's CA friendly Name", "Client's (Relying Party) CA Friendly Name", "TLS Certificate", "OCSP Response Status", "Revocation Status", "Revocation Source", " Identify Target by certificate's Serial No", " Identify Target by importing certificate" "Request Time From" and "Request Time To". If a search is based on multiple values, then these will be combined together using the “AND” operand, and thus only records that meet all the criteria will be presented. Using this search filter you can create custom reports based on:
- Which target certificates were validated
- Which target CA was involved
- Which relying party made the requests
- Specific date ranges
- Which source was used for revocation
Clicking on the Customize Columns button on OCSP Transactions Log Viewer displays following screen:
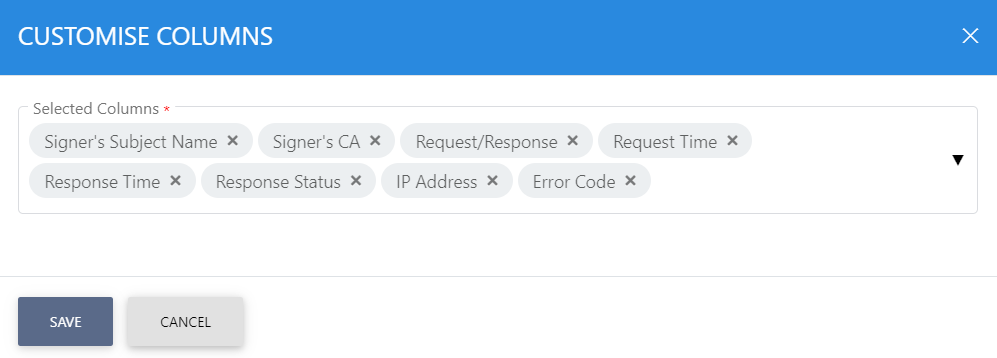
By default few columns are in the "Selected Columns" list. In order to hide a column move the required column to "Available Columns" list.
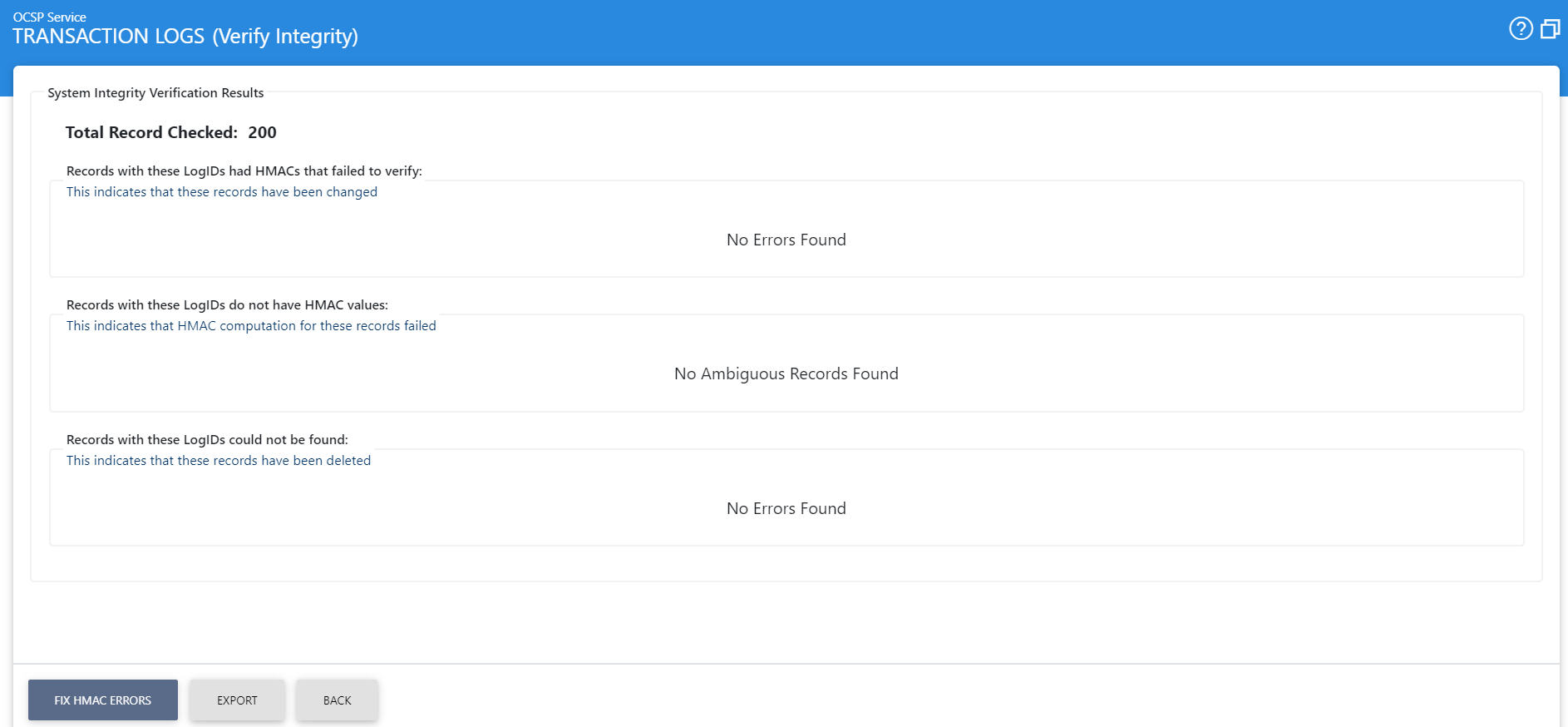
Each log record within the database is protected with an HMAC checksum to detect any intentional or accidental modification of records. Clicking Verify Integrity button verifies the log integrity and generates a report as shown below:
Click on the Export Logs button to export the request/response to a network file.
|
|
The transaction logs are not exported according to the applied filter/search, they are exported as a complete zip file. |
Clicking the Fix HMAC button will re-calculate the HMAC for tampered transaction logs records for this module.
Note: This option will not detect the unauthorized deleted records but it will only fix the unauthorized modifications and/or ambiguous records for which HMAC value is not present/incorrect.
|
|
After an OCSP transaction has been performed, it takes 10 seconds (approx.) to display the transaction details in the Transaction Log Viewer. |
OCSP transactions log can be exported to physical drive using Export Logs button. You can either export all OCSP logs or specific OCSP logs based on provided search criteria. Note when exporting log records, the original records remain in the database (i.e. they are not removed as part of the export function). In case of auto-archiving (explained later) the archived records will by default also be removed from the database. Therefore use auto-archiving if you want to trim your database.
It is also possible to view the low-level details of how a particular transaction was processed by clicking the link in Log ID column. Once clicked, the following screen will be displayed:
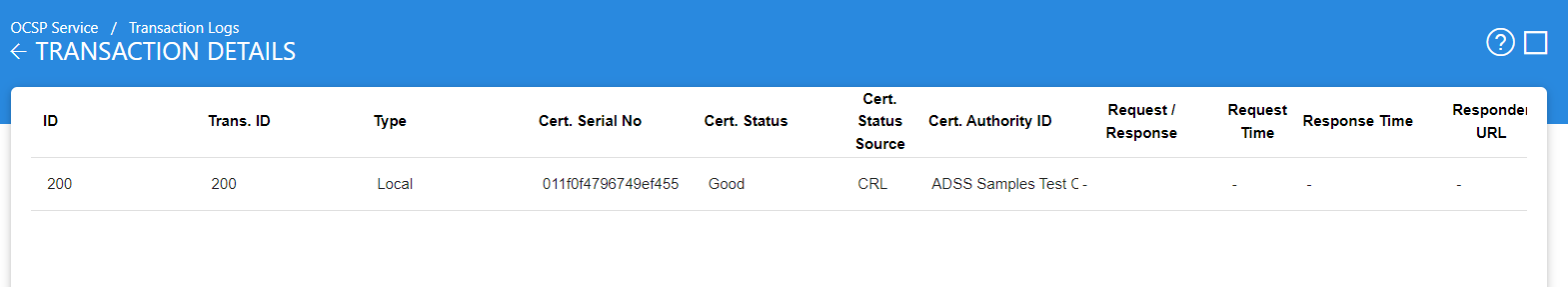
The columns in this table are as follows:
|
Items |
Description |
|
ID |
This is a unique number for of each step in the signature verification process. For example, there may have been multiple certificates requested for status checking within a single OCSP request. In this case the validation of each certificate will be shown with a unique log ID. |
|
Trans. ID |
This is the unique ID assigned to the selected OCSP transaction. |
|
Type |
This column specifies how the revocation of the target certificate was performed i.e. locally or was the request forwarded to some peer OCSP responder. |
|
Cert. Serial No. |
Serial number of the target certificate whose revocation was checked. |
|
Certificate Status |
Certificate status of the target certificate (Good, Revoked or Unknown). |
|
Certificate Status Source |
This column provides a source through which revocation is provided for a certificate. |
|
Certificate Authority ID |
This column provides the name of the required certificate authority (CA) that has issued the certificate. |
|
Request/Response |
This column provides a link to view the OCSP request that was received or the OCSP response sent by the OCSP service. |
|
Request Time |
Time when the request was made to the OCSP Service. |
|
Response Time |
Identifies the time when the response was sent by the OCSP service. |
|
Responder URL |
This column specifies the responder address if a peer OCSP responder was invoked for checking the revocation status. |
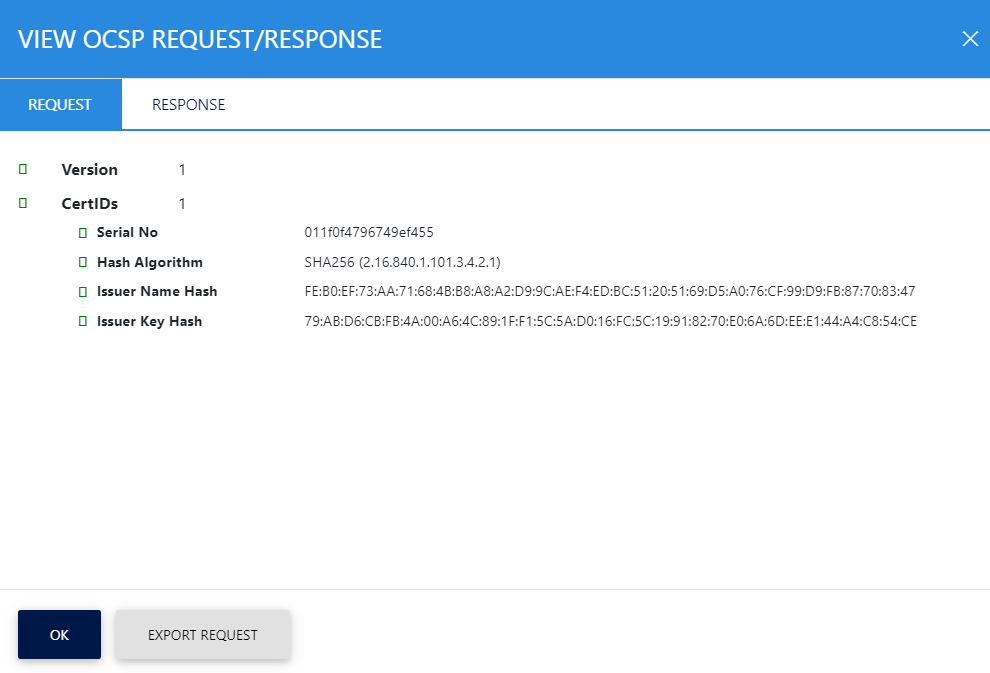
Clicking on either View link within the Request column or the Show Request button shows the OCSP request involved in this transaction as shown below:
Clicking on either View link within the Response column or the View Response button shows response for the OCSP transaction as shown below:
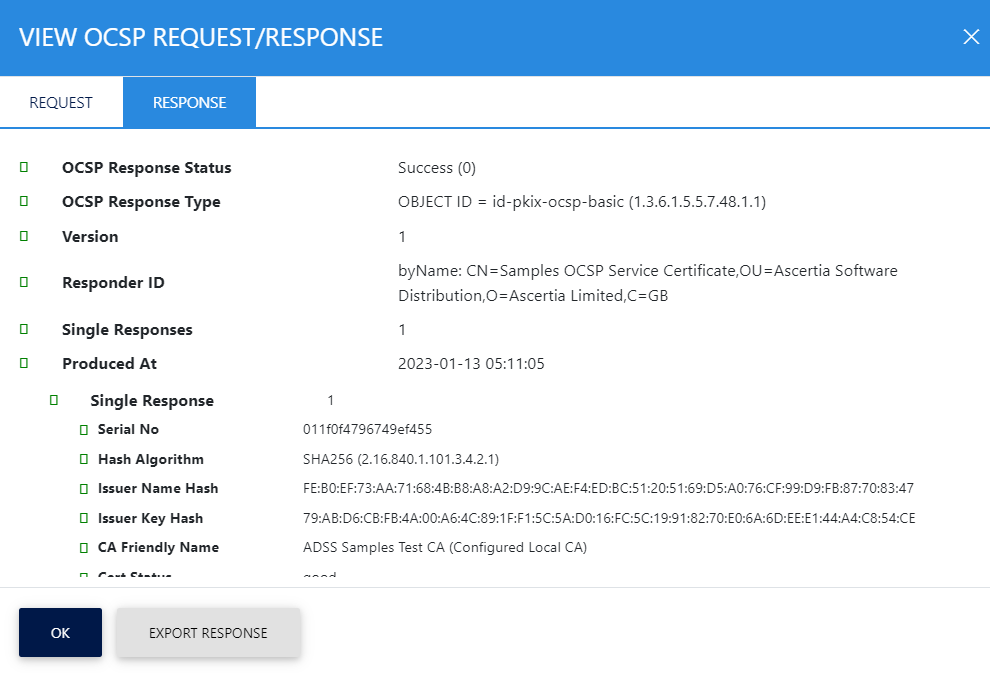
Click on the relevant export button to export the OCSP request/response on the physical drive.
See also
Support for Multiple Trust Models
Multiple CA and Unique Certificate Validation Policies
Configuring the OCSP Service
General Policy Settings
Forwarding Modes
Access Control
Transactions Logs
Logs Archiving
Alerts
Advanced Settings
Optimising ADSS OCSP Server Performance
Operating OCSP Service in FIPS 201 Compliant Mode

