SAM Service
The following configurations relating to the SAM Service can be made within Client Manager:
- Allow the client to access the ADSS SAM Service.
- Assign the SAM Profiles which can be accessed by this client.
- Configure a default SAM Profile for this client.
Once a client is registered, permissions to access the SAM service can be granted by editing this client. On the edit screen, clicking on the SAM Service link at the top of the page shows the following screen:
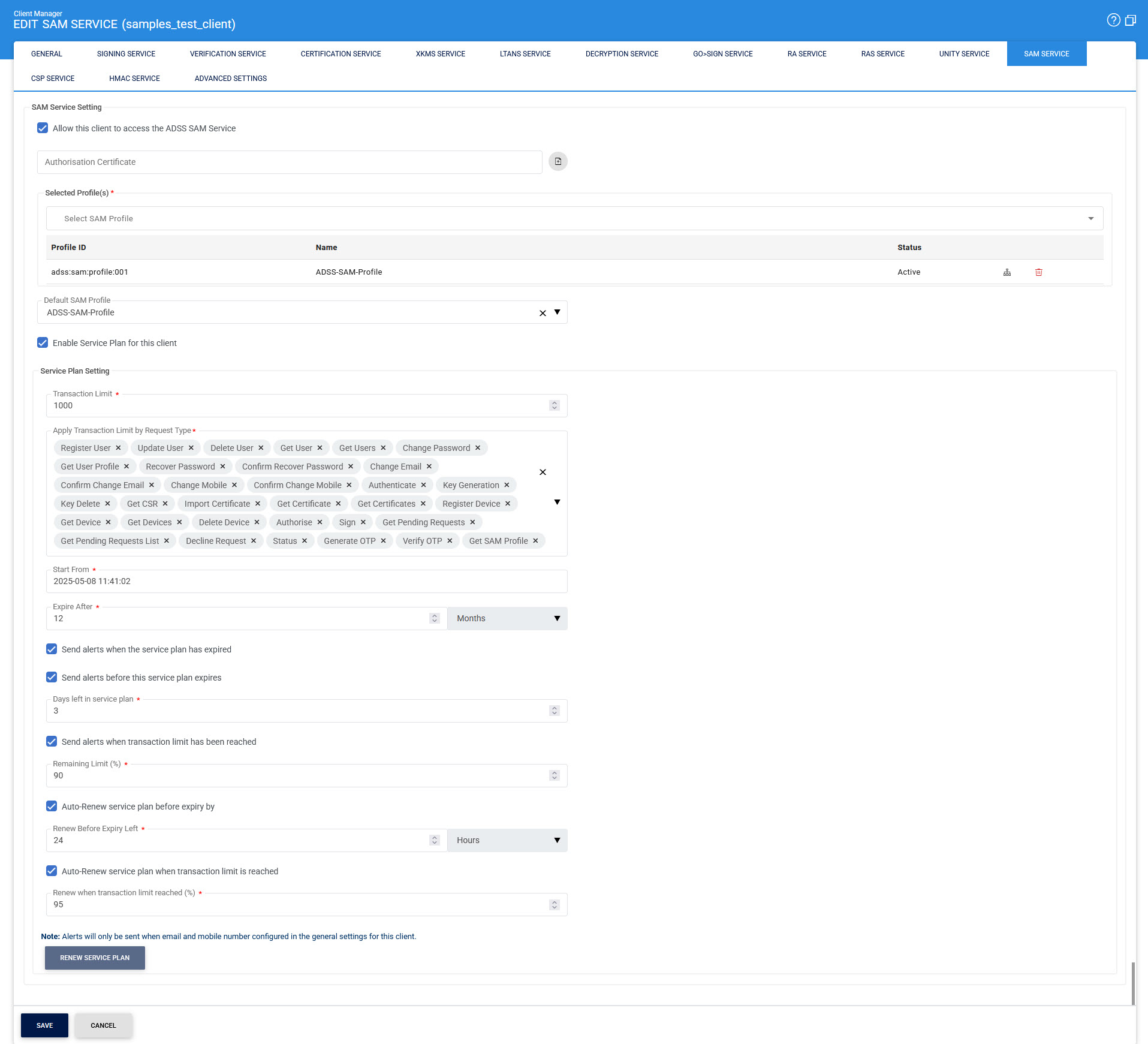
The configuration items are as follows:
|
Items |
Description |
||
|
Allow this client to access the ADSS SAM Service |
Enable the 'Allow this client to access the ADSS SAM Service' checkbox to grant the client permission to make SAM Service requests to the ADSS Server. If the application also requires access to additional ADSS services (e.g., verifying signed documents or generating and certifying user signing keys), ensure to navigate to the relevant sections (e.g., Verification Service, Certification Service) and grant the necessary permissions for those services. |
||
|
Authorisation Certificate |
While the SAD is typically signed by the Go>Sign mobile application, there are scenarios where it may be signed using a key managed by the business application. These scenarios include:
|
||
|
Selected SAM Profile |
The next step is to specify which SAM profiles, configured within the ADSS SAM Service, should be accessible to the client. By default, all existing SAM profiles are made available to newly registered clients. However, different clients may require access to specific SAM profiles. To grant access to a particular SAM profile, move the desired profile from the Available SAM Profiles list (on the left) to the Selected SAM Profiles list (on the right) by using the >> button. Clients can only access the SAM profiles listed in the Selected SAM Profiles section. To revoke access to a SAM profile, use the << button to move it back to the Available SAM Profiles list. |
||
|
Profile Usage Map |
The Profile Usage Map button provides an overview of which profiles are being used by which clients. |
||
|
Default SAM Profile |
The Default SAM Profile defines which profile to use in case the request message from this client does not reference any specific SAM profile. |
||
|
Enable Service Plan for this Client |
Enabling this option allows the client to access service plan configuration settings. |
||
|
Transaction Limit |
This field lets the operator define the maximum number of transactions the client can perform.
|
||
|
Apply Transaction Limit by Request Type |
This option allows the operator to set transaction limits based on specific request types. For the SAM Service, the available request types include:
|
||
|
Start From |
Select the starting date when the service plan will be started. |
||
|
Expire After |
Define the duration after which the service plan will expire. Users can specify the expiry period by selecting a number of days, months, or years. |
||
|
Send alerts when the service plan has expired |
By enabling this checkbox, an alert will be sent to the client when the plan has expired. |
||
|
Send alerts before this service plan expires |
When enabled, this checkbox activates a field where the user can specify the number of days before the plan’s expiry to send an alert to the client. |
||
|
Send alerts when transaction limit has been reached |
Enabling this option sends an alert to the client when the transaction limit reaches a specified percentage, as defined by the user. |
||
|
Auto-Renew service plan before expiry by |
This option allows the user to configure automatic renewal of the service plan before its expiry by specifying a time frame in hours, days, or months. |
||
|
Auto-Renew service plan when transaction limit is reached |
Enabling this option sets the service plan to renew automatically once the transaction limit reaches the defined percentage. |
||
|
Renew Service Plan |
This button allows the user to manually renew the service plan. Note that this button is disabled if auto-renewal options are selected. |
||
|
EST Client Authentication Settings |
When the client communicates with the ADSS Server over mutual TLS and the Require HTTP Basic Authentication with TLS Client Authentication checkbox is enabled, both the TLS client authentication certificate and the client credentials (ClientID and Client Secret) are required for identifying and authenticating the client registered in the Client Manager. However, if the client does not use mutual TLS and this option is enabled, the checkbox will be disregarded, and the client will instead be authenticated using HTTP Basic authentication. |
|
|
The alert checkboxes will trigger alerts only if the client has configured both an email address and a mobile number in general settings for the client. |
Click the Save button when the list is updated to store the changes.
|
|
Whenever configurations are updated on this page remember to restart the SAM Service and have the changes take effect. |
See also
Signing Service
Certification Service
Verification Service
Go-Sign Service
SAM Service
RAS Service
CSP Service
Unity Service
Advanced Settings

