External CAs
External CA could be used which may be operated internally by the organisation operating the ADSS Server or alternatively it may be a CA operated by an external managed certificate service provider.
|
|
Integration of ADSS Server with other External CAs is possible because standard data structures are used by ADSS Server (e.g. PKCS#10 for certificate requests and PKCS#7 for certificate responses. |
When using an external CA to issue certificates for keys generated by the ADSS Certification Services then the workflow is expected to be as follows:
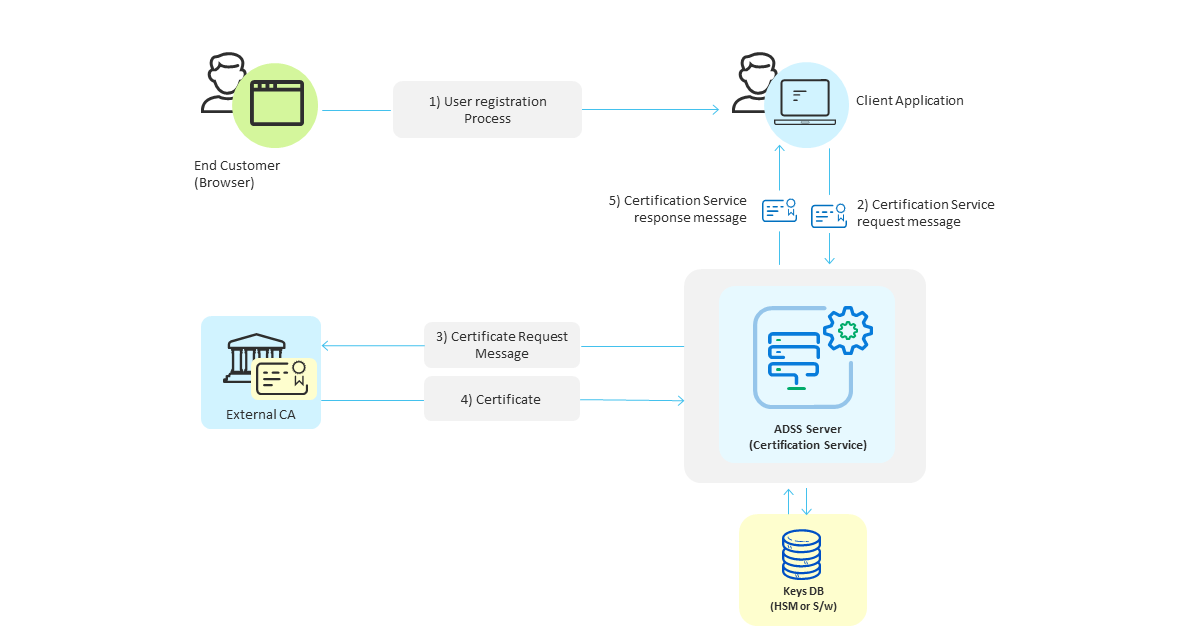
- Initially end-users interact with an online business client application as part of a registration process that is outside the scope of the ADSS Server.
- Once the registration is complete the business application makes a request for key/certificate generation for the user and sends a certification service request message to ADSS Server. This request message identifies the certification profile to be used (configured on ADSS Server) and a unique authorisation code for protecting/accessing this key pair (i.e. a pass-phrase that the user will probably be asked to provide when being asked to confirm signing actions).
- The ADSS Certification Service generates the keys and then sends a certificate request message in PKCS#10 format to the external CA configured in the certification profile.
- The external CA should respond and provide the certificate in PKCS#7 format back to ADSS Server. ADSS Server stores this with the key pair it generated for this user. When keys are being stored within the database, ADSS Server will create a PKCS#12/PFX file which will contain both the private key and this public key certificate. The PKCS#12/PFX file will be encrypted using the authorisation code provided in the original request message. When an optional HSM is used the keys are stored in raw format and an authorisation code is not required, the HSM security features protect the private key in a secure tamper-resistant enclosure. This is the recommended way of protecting private keys in environments which demand stronger security.
- The ADSS certification service sends a response message back to the business application confirming the results of the operation.
The ADSS Developers Guide explains the XML schema used for both the certification service request messages and the certification service response messages.
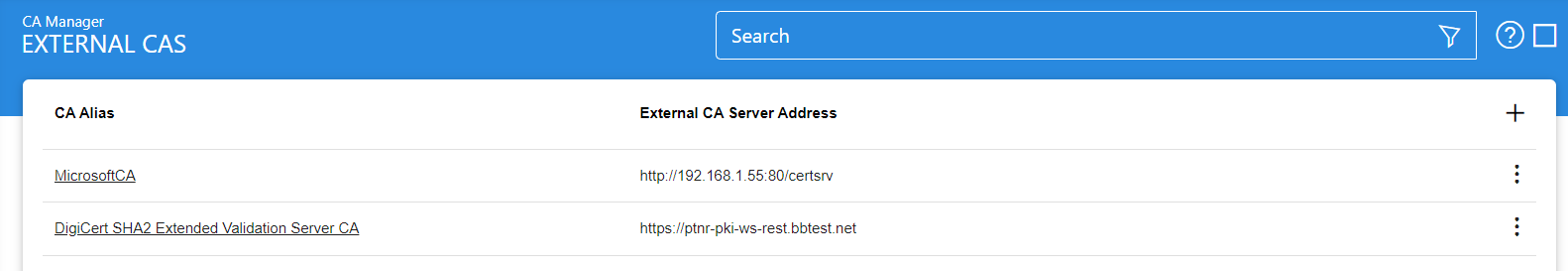
To configure the settings for external CAs, click the Configure External CAs button in the screenshot below. This shows a list of configured external CAs:
Issued Certificates
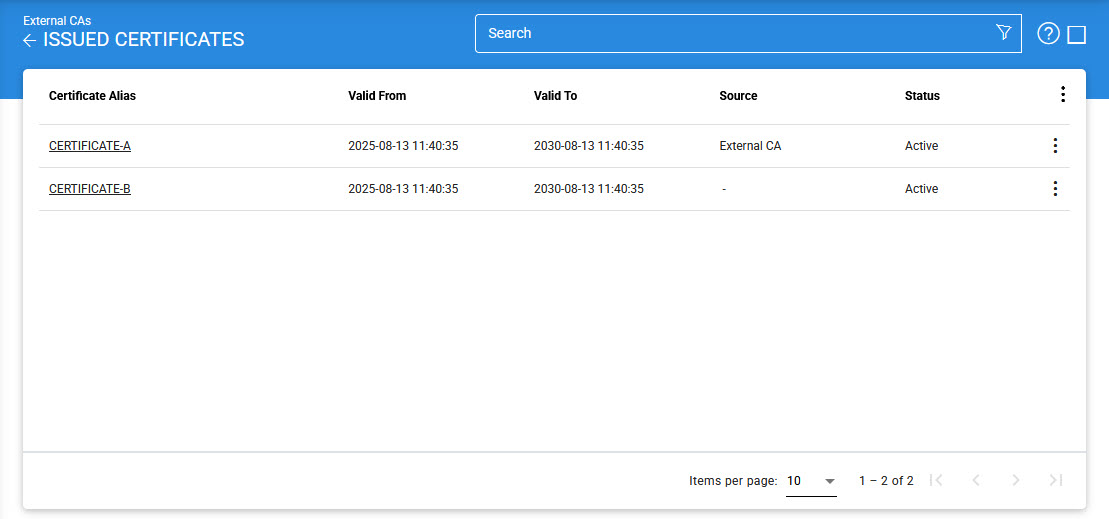
By clicking on the Issued Certificate button after selecting the relevant External CA, the following screen will be displayed where all the certificates issued by this CA are shown:
|
|
This screen shows certificates issued by Key Manager, Certification Service and Manual Certification while the Certification Service's Issued Certificate sub module only shows the certificates issued by the Certification Service. |
When users click the ellipsis at the end of a row, the Import Certificate option becomes available. This feature allows users to bring in certificates that were originally issued by an external CA and manage them in ADSS Server through Web RA, in the same way as locally issued certificates. To perform the import, users need to upload two files generated by the Import Certificate Utility: an Excel file containing the certificate details and a ZIP file with the corresponding certificate files. During the process, each certificate is automatically associated with the correct External CA, client, and certification profile. Once imported, the certificates appear under the selected External CA and can be fully managed. Users can then carry out lifecycle actions such as revoking, reinstating, or deleting certificates directly through Web RA.
Clicking on the Import Certificate button will display the following screen:
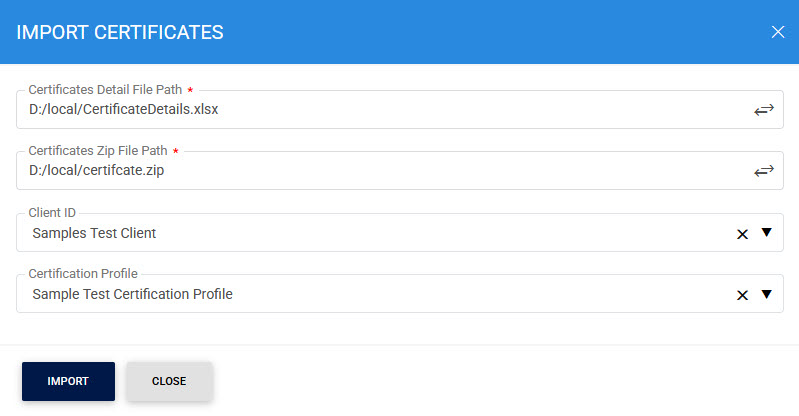
The items in the above screen are described below:
|
Items |
Description |
|
Certificate Details File Path |
Enter the path to the Excel file (.xlsx) that lists the certificates you want to import. This file is created by the Import Certificate Utility and includes the important details needed to register each certificate under the selected External CA. Make sure you use the details file generated for the same set of certificates you are importing. |
|
Client Zip File Path |
Enter the path to the ZIP file that contains the actual certificate files mentioned in the details file. This ZIP is generated by the Import Certificate Utility at the same time as the Excel file. The system reads this ZIP to match and attach the correct certificate file to each record in the details spreadsheet. |
|
Client ID |
Choose the client (such as an organization or application) that will be linked to the imported certificates. Connecting certificates to a client makes sure that client applications (like Web RA) can later manage them, for example, by revoking or reinstating them. |
|
Certification Profile |
Choose the certification profile for the imported certificates. This links the certificates to the correct rules and usage settings in the ADSS Server. It also ensures that client applications can manage the certificates properly, including life-cycle actions like revocation. |
|
|
The Client ID and Certification Profile fields are optional. However, if they are not provided, the certificates will be imported, but revocation actions will not be possible. |
You can select a certificate, and then either View, Revoke or Delete it. Clicking on Revoke button will show the following screen where invalidity date, revocation code and hold instruction code can be provided before revoking the certificate:
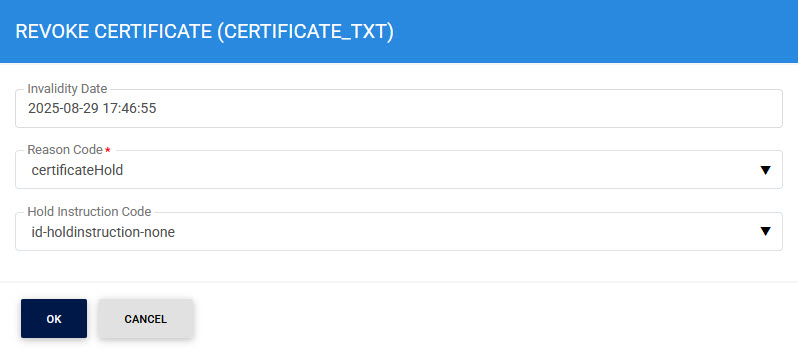
|
|
A certificate revoked with the certificateHold instruction code can be activated later on by using the Reinstate button. |
To view the linting report for a selected certificate, click on the vertical ellipsis next to the row on the main screen and select the Linting Report option. This action will open a new screen where you can choose the desired External Script Linter from the drop-down list configured under Global Settings > External Script Linters:
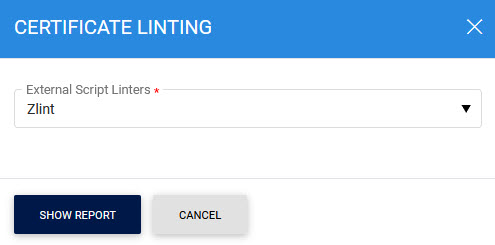
After selecting the linter, click Show Report to display the linting details of the certificate:
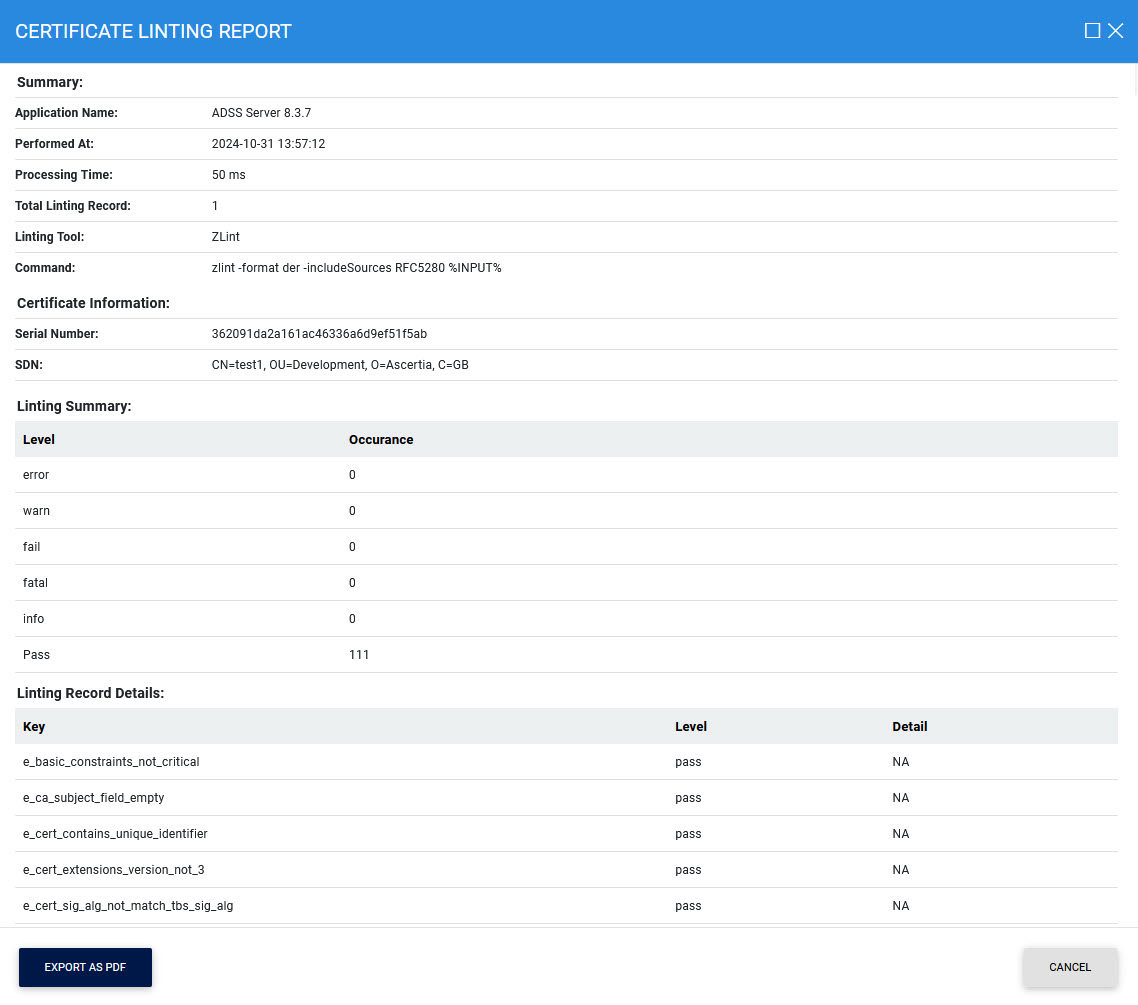
Additionally, you can export the report in PDF format by clicking the Export PDF button.
By clicking on the Advance Search button on Issued Certificates main page will display following screen:
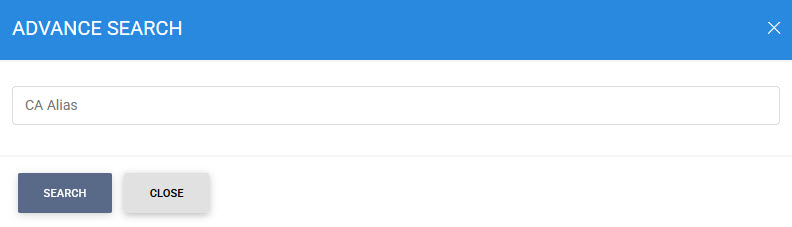
|
|
In case of External CAs, upon revoking an issued certificate, the ADSS Server marks that certificate status to revoke in it's internal database but not in CAs database. That is because the ADSS Server does not support sending automated revocation request to External CAs. Hence, the user need to send a formal manual request to External CA by following it's procedure in order to revoke the certificate in its database. |
See also

