Thales Luna K7 Cryptographic Module
The Thales Luna K7 Cryptographic Module is Common Criteria certified HSM according to the Protection Profile (PP) EN 419 221-5 "Cryptographic Module for Trust Services". This HSM can be used with Ascertia SAM appliance to produce qualified remote signatures and seals.
A new Crypto Source can be created in ADSS Server > Key Manager. Press the New button in the Crypto Source Screen to do so. The following form is presented:
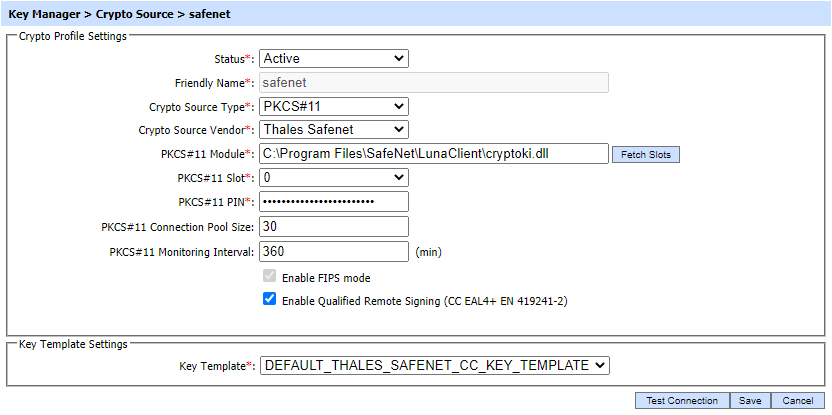
The above page is described here:
| Item | Description |
| Status |
Set the status of this crypto profile. If the status is set to Inactive then it can not be used to generate or read the keys for cryptographic operations. |
| Friendly Name | Enter a friendly name for this HSM device. The name should be unique within this ADSS Server environment. Use a meaningful name for easy reference, e.g. Thales_Luna etc. |
| Crypto Source Type | Select the option PKCS#11 from the supported options. PKCS#11 offer full support including management of key generation and PKCS#7/CSR handling. |
| Crypto Source Vendor |
Select the option Thales as Crypto source vendor |
| PKCS#11 Module |
Enter the PKCS#11 driver library file name/complete path for this HSM device.
Note: To find the library name of your device, refer to the documentation of the driver or contact the HSM vendor support to find the library name.
|
| Fetch Slots |
When this button is clicked then available slots within the PKCS#11 HSM are shown. The list of available slots will be shown in the next field i.e. Fetch Slots
Note: If no slots are shown, then the HSM may not be initialized correctly – consult the HSM installation & usage guide.
|
| PKCS#11 Slot | Select the appropriate PKCS#11 slot. The drop down lists all the available slots for the configured PKCS#11 module. |
| PKCS#11 PIN |
Enter the PIN or password of the Slot initializer user e.g. USR_0000
Note: The PIN is held securely in ADSS Server.
|
| PKCS#11 Connection Pool Size | Enter the number of connections that will be maintained at any given time for this PKCS#11 device. Default value is 30. |
| PKCS#11 Monitoring Interval |
Enter the monitoring time interval in minutes to periodically check whether the PKCS#11 device is alive. If it finds the device is not alive/available due to any reason then an email alert could be sent if Hardware crypto source monitoring is enabled in Key Manager > Alerts page.
Note: To generate the notification alerts, alerts should be enabled at Global Settings > Alert Settings page. |
| Test Connection | This button is used to test communications with the configured hardware device. |
| Enable FIPS Mode | Thales Luna K7 is FIPS compliant device and this mode must be enabled by selecting this checkbox. |
| Enable Qualified Remote Signing | Enable this checkbox to allow EU eIDAS compliant Remote Qualified Signatures to be produced. The signatures are created on the Thales Luna K7 EN 419 221-5 Common Criteria certified HSM. |
| Key Template | The drop-down contains a list of key templates configured in Key Templates sub-module. Here, Thales Safenet CC certified key template will be attached from the drop-down. ADSS Server provides a default key template for Thales Safenet CC certified HSM i.e. 'DEFAULT_THALES_SAFENET_CC_KEY_TEMPLATE'. The operator can either attach the default key template or can create a new Thales Safenet CC certified key template with desired configurations. |
Whenever the crypto source is changed, it is mandatory to re-start the ADSS Server Windows or Unix services.
See also