CMS/CAdES Signing Attributes
When CMS or CAdES signatures are selected the following Signing Profile options are presented (each option is discussed in the table below):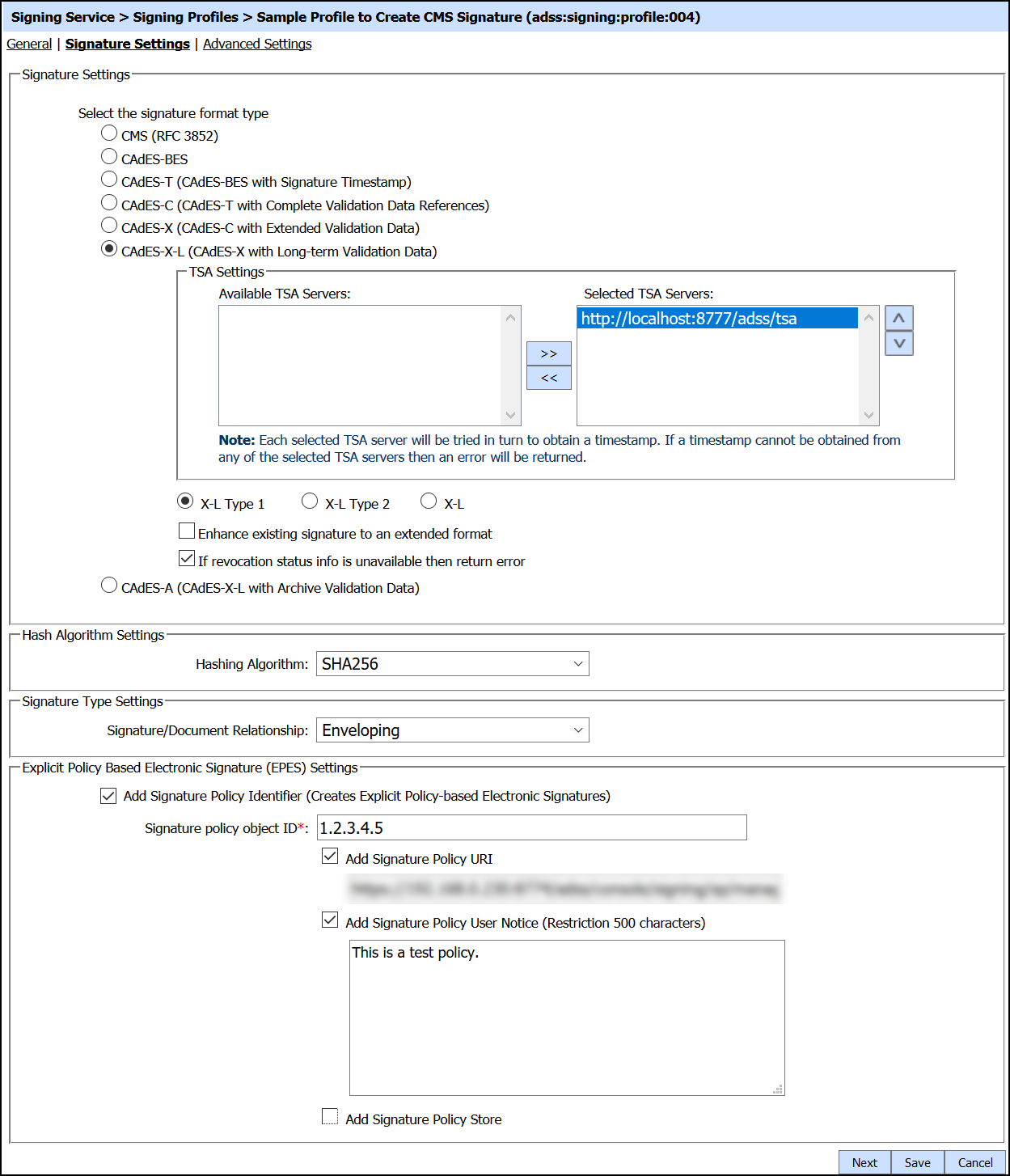
The configuration items are as follows:
| Items | Description |
| Signature Settings |
Select the signature format to be produced. For more details see the section Supported Signature Types. |
| Timestamp (TSA) Settings |
Select the required timestamp authority (or potentially several authorities) from the list of pre-registered TSAs. The configuration of TSA address(es) is described in this section: Configuring Time Stamp Authorities (TSA).
Note: If the signing certificate Issuer CA (defined in Trust Manager) has one or more associated TSAs then these settings override the TSAs defined in this signing profile.
|
| Signature Conversion |
When the signing service receives data or a hash to sign, this option is ignored. This is a special option to be used only when the business application send data with a basic signature to the service in order to have it extended to a long-term format. The recommended approach is to use the Verification Service for this so that the signature can be checked first and then extended.
If this option is to be used then the following signatures can be converted as follows:
It is generally recommended to use the ADSS Server Verification Service to verify signatures and then extend them to other formats. |
| Signature Grace Period |
This will define how long ADSS Server should wait after the signing time indicated in the signature (either by TSA or by signer's local time) before converting the basic signature to an advanced signature.
Note: The default value set to '0' which defines there is no signature grace period and the signature is to be converted immediately to an advanced signature type as requested in the API call.
|
| Revocation Status Information Unavailable Error |
If one of following signature types are selected:
Then an extra check box is offered to decide if ADSS Server should return an error if it cannot embed the revocation information when creating the Long-Term signature.
Such
signatures require embedded status/ revocation information for the
signer's certificate chain. This is useful to stop basic signatures
being created when a communication failure prevents revocation
information being obtained from external resources. If this check box
is not selected then the signature will be produced but it may not
contain the embedded revocation if this was unavailable at the time of
signing, e.g. if the relevant OCSP is not responding or if the dynamic
CRL is unavailable. ADSS Server is generally configured to cache CA CRLs
locally and it also has a short-life cache for dynamic CRLs and OCSP
responses.
Note: It is recommended you always tick this box.
|
| Hashing Algorithm |
Select which hash algorithm to use as part of the signature creation process. The following algorithms are supported:
SHA256 is recommended. |
| Signature/Document Relationship |
This defines how the signature is to be provided. Either the signature can be wrapped around the data or provided separately. The following options are supported:
|
| EPES signature |
Explicit Policy Based Electronic (EPES) signature settings are only available for the CAdES signature types. By enabling the check box Add Signature Policy Identifier, the signing profile can be used to produce (EPES) signatures where a signature policy OID, URI and user notice are added in the digital signature as specified below. 1. Signature Policy Object ID
Provide the Signature Policy OID to be added for EPES signatures.
2. Signature Policy URI
Provide the Signature Policy URI to be added for EPES signatures.
If there is no Policy URI defined inside the signing profile then EPES configurations should be made in policy.properties file located at: [ADSS Installation Directory]/service/
Open this file in any text editor and enter policy OID and path to the policy document
e.g. 1.2.3.4.5 = "F:/Policy_File"
The ADSS Signing Service can retrieve the signature policy document in either one of the following ways:
Using a Policy URI defined in signing profile. The ADSS Signing Service will use this policy URI to retrieve the online available policy document and its hash value will be calculated and embedded in the signed properties of the signature.
Using locally configured signature policy document. The ADSS Signing Service will use this text file pointer to retrieve the locally-saved policy document, hash and embed it in the signed properties of the signature.
3. Signature Policy User Notice
If this option is selected then you must provide a user notice to be added to the EPES signature.
|
See also