Multiple CA and Unique Certificate Validation Policies
The marketing name for ADSS Server configured to operate just as an OCSP Validation Authority is ADSS OCSP Server. ADSS Server can provide multiple signing, verification and validation services concurrently.
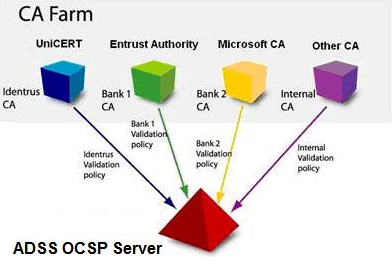
A single installation of ADSS OCSP Server can act as a “Validation Hub” and respond on behalf of multiple Certification Authorities (sometimes referred to as a CA Farm). Each CA can have a unique certificate validation policy assigned to it. The Policy Management module can be used to configure the following aspects of a CA validation policy:
-
Policy for gathering revocation information (e.g. how the revocation information will be retrieved, how often, from where, how to deal with failures, etc.)
-
Policy for Peer OCSP responder communication (e.g. is peer OCSP forwarding allowed, how is the peer OCSP responder identified, how is the peer OCSP request formatted, etc.)
-
Policy for revocation checking of OCSP requesters and Peer OCSP responders (e.g. is revocation checking performed for these entities, and if so, how, etc.)
Further to this each CA can use its own OCSP response signing key and associated certificates so that there is no sharing of cryptographic material between different CAs.
The validation policy for each CA within ADSS OCSP Server defines how often the CRL information is to be downloaded from either one or more LDAP directories or one or more HTTP server locations. As a project option support for IETF CMP revocation messages can be added to ADSS Server. Real time validation information can also be accessed if this is supported by the CA, see Real Time Revocation.
The figure below illustrates a single installation of ADSS OCSP Server responding for multiple CAs in a CA Farm - supporting a unique certificate validation policy for each:
ADSS OCSP Server is designed to be CA-product and vendor neutral.
See also