Utimaco CryptoServer CP5 HSM
The Utimaco CryptoServer CP5 HSM is Common Criteria-certified according to the eIDAS Protection Profile (PP) EN 419 221-5 "Cryptographic Module for Trust Services".
Currently, only the ADSS SAM Appliance with embedded CryptoServer CP5 PCI-e HSM is covered by the the Common Criteria EAL4+ certification process.
In order to configure and use the CryptoServer CP5 you must generate and place the HSMAuthKey.key file at location: [ADSS Server Installation Directory]/conf/hsm/utimaco. It is required to establish the mutually authenticated, secure messaging session for communication between the CryptoServer CP5 and ADSS Server.
|
|
The key file is generated using the Utimaco CP5 client software. This file must be named "HSMAuthKey.key" before copying to the ADSS Server file structure. If necessary, rename the file after generating it. |
Once the prerequisites step above has been completed, a new Crypto Source can be created in ADSS Server > Key Manager. Press the New button in the Crypto Source Screen to do so. The following form is presented:
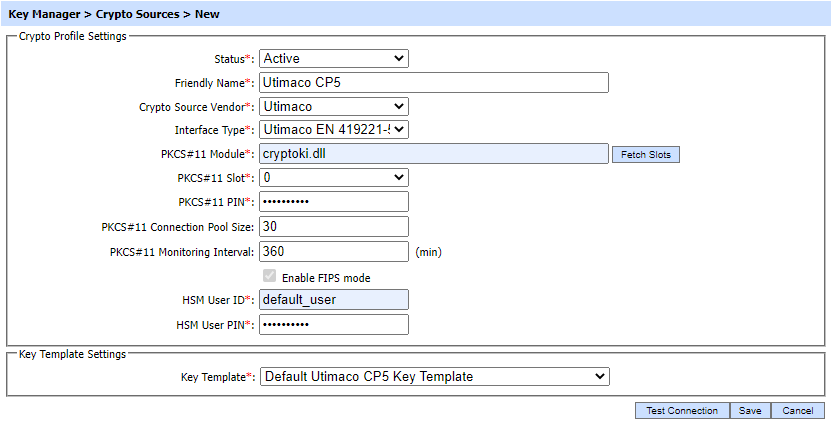
The above page is described here:
|
Items |
Description |
|
Status |
Set the status of this crypto profile. If the status is set to Inactive then it can not be used to generate or read the keys for cryptographic operations. |
|
Friendly Name |
Enter a friendly name for this HSM device. The name should be unique within this ADSS Server environment. Use a meaningful name for easy reference, e.g. UTIMACO_Appliance_SAM etc. |
|
Crypto Source Vendor |
Select the option UTIMACO as Crypto source vendor. |
|
Interface Type |
This drop-down will allow the operator to select the interface type for the UTIMACO crypto source vendor i.e. either Utimaco PKCS#11 or Utimaco EN 419221-5. Both are explained below:
|
|
PKCS#11 Module |
Enter the PKCS#11 driver library file name/complete path for this HSM device. Note: To find the library name of your device, refer to the documentation of the driver or contact the HSM vendor support to find the library name. |
|
Fetch Slots |
When this button is clicked then available slots within the PKCS#11 HSM are shown. The list of available slots will be shown in the next field i.e. Fetch Slots Note: If no slots are shown, then the HSM may not be initialized correctly – consult the HSM installation & usage guide. |
|
PKCS#11 Slot |
Select the appropriate PKCS#11 slot. The drop down lists all the available slots for the configured PKCS#11 module. |
|
PKCS#11 PIN |
Enter the PIN or password of the Slot initializer user e.g. USR_0000 Note: The PIN is held securely in ADSS Server. |
|
PKCS#11 Connection Pool Size |
Enter the number of connections that will be maintained at any given time for this PKCS#11 device. Default value is 30. |
|
PKCS#11 Monitoring Interval |
Enter the monitoring time interval in minutes to periodically check whether the PKCS#11 device is alive. If it finds the device is not alive/available due to any reason then an email alert could be sent if Hardware crypto source monitoring is enabled in Key Manager > Alerts page. Note: To generate the notification alerts, alerts should be enabled at Global Settings > Alert Settings page. |
|
Test Connection |
This button is used to test communications with the configured hardware device. |
|
Enable FIPS Mode |
CP5 HSM is FIPS compliant device and this mode must be enabled by selecting this checkbox. |
|
HSM User ID |
Specify the User ID for the Crypto User (For Restore Key) e.g. USR1_0000. |
|
HSM User PIN |
Specify the PIN for above configured Crypto User. |
|
Key Template |
The drop-down contains a list of key templates configured in Key Templates sub-module. Here, Utimaco CC certified key template will be attached from the drop-down. ADSS Server provides default key template for Utimaco CC certified HSM i.e. 'Default Utimaco CP5 Key Template'. The operator can either attach the default key template or can create a new Utimaco CC certified key template with desired configurations. |
|
|
Whenever the crypto source is changed, it is mandatory to re-start the ADSS Server Windows or Unix services. |
See also
PKCS#11 Standard
Thales Luna K7 Cryptographic Module
nCipher nShield Solo XC Cryptographic Module
Azure Key Vault
AWS CloudHSM
MS-CAPI/CNG
Importing Existing Keys
