Certification Profiles
An ADSS Service Profile is created in ADSS Web RA to configure ADSS Profiles (Certification and/or CSP) to issue different types of certificates for the ADSS Web RA users. In other words, an ADSS Server profile (Certification and/or CSP) is actually created at the ADSS Server end, and it is referred in the ADSS Web RA Admin for its implication.
The ADSS Certification Profiles entail all the complex configurations and business requirements (i.e. CA details, Key Algorithm, Validity, etc.) to issue corresponding certificates for the ADSS Web RA users, however, ADSS Web RA only uses these profiles to keep the things simple.
How it Works?
ADSS Web RA and ADSS Server supports the following certificate types:
- Signing the CSR only (the CSR is generated in another application e.g. IIS, a device etc.). The following configurations are required for this:
- A Client must be registered in ADSS Server Client Manager
- The Client must be configured in the ADSS Web RA connector of ADSS Server
- A Certification Profile must be created in the ADSS Certification Server
- A Certification Profile must be created in the ADSS Web RA to map the ADSS Server Certification Profile
- The ADSS Web RA Certification Profile must be configured in the Service Plan
- Generating the key pair on client side and signing the CSR
- A Client must be registered in ADSS Server Client Manager
- The Client must be configured in the ADSS Web RA connector of ADSS Server
- A Certification Profile must be created in the ADSS Certification Server
- A Go>Sign Profile must be created in the ADSS Go>Sign Server of type Certificate Generation
- A Certification Profile must be created in the ADSS Web RA to map the ADSS Server Certification Profile
- The Go>Sign Profile must be configured in the ADSS Web RA Certification Profile
- The ADSS Web RA Certification Profile must be configured in the Service Plan
- Server side key generation for remote authorized signing
- Client must be registered in ADSS Server Client Manager
- The Client must be configured in the ADSS Web RA connector of ADSS Server
- A SAM Profile must be created in the ADSS SAM Server
- A RAS Profile must be created in the ADSS RAS Server
- A CSP Profile should be created in the ADSS CSP Server (only needed if you want to use the CSP service. Also, a CSP profile should be created in ADSS Web RA to map the ADSS CSP Profile.)
- A Certification Profile must be created in the ADSS Certification Server
- A Certification Profile must be created in the ADSS Web RA to map the ADSS Server Certification Profile
- The Go>Sign Profile must be configured in the ADSS Web RA Certification Profile
- The ADSS Web RA Certification Profile must be configured in the Service Plan
Create a Certification Profile in ADSS Web RA
- Click Configurations from the left menu.
- Click ADSS Service Profiles.
- Click
 from the grid header.
from the grid header. - A dialog will appear to add the profile details. The ADSS Service Profile dialog consists of two screens, i.e. Basic Information, Profile Settings, Details. Authentications, Advance Settings. Specify the basic information and click Next to move to the next screen.
- Click Finish. A new service profile will be saved and displayed in the list. See the below table for fields description.
|
Basic Information |
|
|
Field |
Description |
|
Name |
Specify a unique name for this connector, i.e. My ADSS Server. This connector will be used in the ADSS Service Profiles. |
|
Description |
Specify any description related to this certification service profile. |
|
Active |
Tick this check box to activate this connector. Inactive connectors cannot be configured in the Certification or CSP Profiles. |
|
Profile Settings |
|
|
Field |
Description |
|
ADSS Service |
This field will display the ADSS Services (i.e. Certification Service and CSP Service) that are available for ADSS Web RA. Select the one for which this service profile is being created, i.e. Certification Service. |
|
ADSS Certification Server |
This field will display the list of active ADSS connectors in ADSS Web RA. Select the one to use for this certification service profile. |
|
ADSS Certification/CSP Profile |
Specify the ID or name of the profile that has been created in the ADSS Certification/CSP Service for ADSS Web RA, e.g. adss:certification:profile:001 |
|
Certificate Purpose |
It contains a list of standard certificate purposes which actually comes from ADSS, based on selected certification profile. A certificate will be generated based on provided certification profile ID, and the purpose will be the one that is configured under that ADSS Service Profile. Possible certificate purposes could be Document Signing, TLS Server Authentication, Code Signing etc. |
|
Verification Type |
If ADSS Certification Profile is of type TLS Server Authentication then this drop down will appear while creating the profile with following options:
|
|
Enable Device Enrolment |
Tick this checkbox, it is mandatory to select Device Enrolment or it will be a simple certification profile. A drop box will appear, allowing the user to choose and select between SCEP, CMP and ACME according to requirement. |
|
Enable Client Keys |
If configured profile in ADSS Certification profile have fixed RDNs, a check box Enable client keys will appear
|
|
Details |
|
|
Field |
Description |
|
Use this certificate profile to generate keys on smart cards/tokens |
Enable this option if this profile will be used to generate the certificates in the smart card/ token. |
|
Key Algorithm |
Key Algorithm that will be used to generate the key pair in the smart card/token. This configuration is coming from the ADSS Server so it cannot be changed |
|
Key Length |
Key Length that will be used to generate the key pair in the smart card/token. This configuration is coming from the ADSS Server so it cannot be changed |
|
Validity Period Type |
Validity period type can be configured as a Fixed to restrict the enterprise user to change the certificate validity or it can be set as Custom if enterprise RAO allow an enterprise user to set validity period while creating a certificate request. These Fixed and Custom values can only be used on ADSS Web RA admin, if the selected ADSS Certification profile has set overridable option in certification profile. It will be shown as Fixed validity period type otherwise. |
|
Validity Period |
The certificate validity period. If the CA profile is configured to use its time instead taking the time from the request then this value will be dropped by the CA server. |
|
Validity Duration |
The time unit of the validity period. It could be minutes, hours, days, months and years. |
|
Authentications - Enable Secondary Authentication for: |
|
|
Field |
Description |
|
New Requests |
If enables then an OTP (One TIme Password) can be set as a second factor authentication, and an enterprise RAO has to provide an OTP to approve new certificate request. The OTP can be received either through SMS or via an email, depending upon the selected profile. In Authentication Profiles list only those profiles are listed for which secondary authentication has configured while creating that authentication profile. See Authentication Profiles section for details. |
|
Revocation Requests |
If enables then an OTP (One TIme Password) can be set as a second factor authentication, and an enterprise RAO has to provide an OTP to approve a certificate revocation request. The OTP can be received either through SMS or via an email, depending upon the selected profile. In Authentication Profiles list only those profiles are listed for which secondary authentication has configured while creating that authentication profile. See Authentication Profiles section for details. |
|
Rekey Requests |
Enable authentication for rekey requests will show in the 'Authentications' section to handle second factor authentications for rekey certificate. This section only shows when the operator has enabled the 'rekey' policy. |
|
Advance Settings |
|
|
Field |
Description |
|
Agreement |
Select a subscriber agreement if Admin wants a user to agree on some terms before submitting a certificate request |
|
Vetting Option |
Select whether vetting is required for this certification service profile or not. Select the "Manual Vetting" option if you require the vetting provision and then select a vetting form from the next appearing field. |
|
Vetting Form |
This field will display the list of active vetting forms. Select the one to use for this certification service profile. |
|
Enable Revocation Vetting |
Tick this checkbox if you want enable vetting for revocation |
|
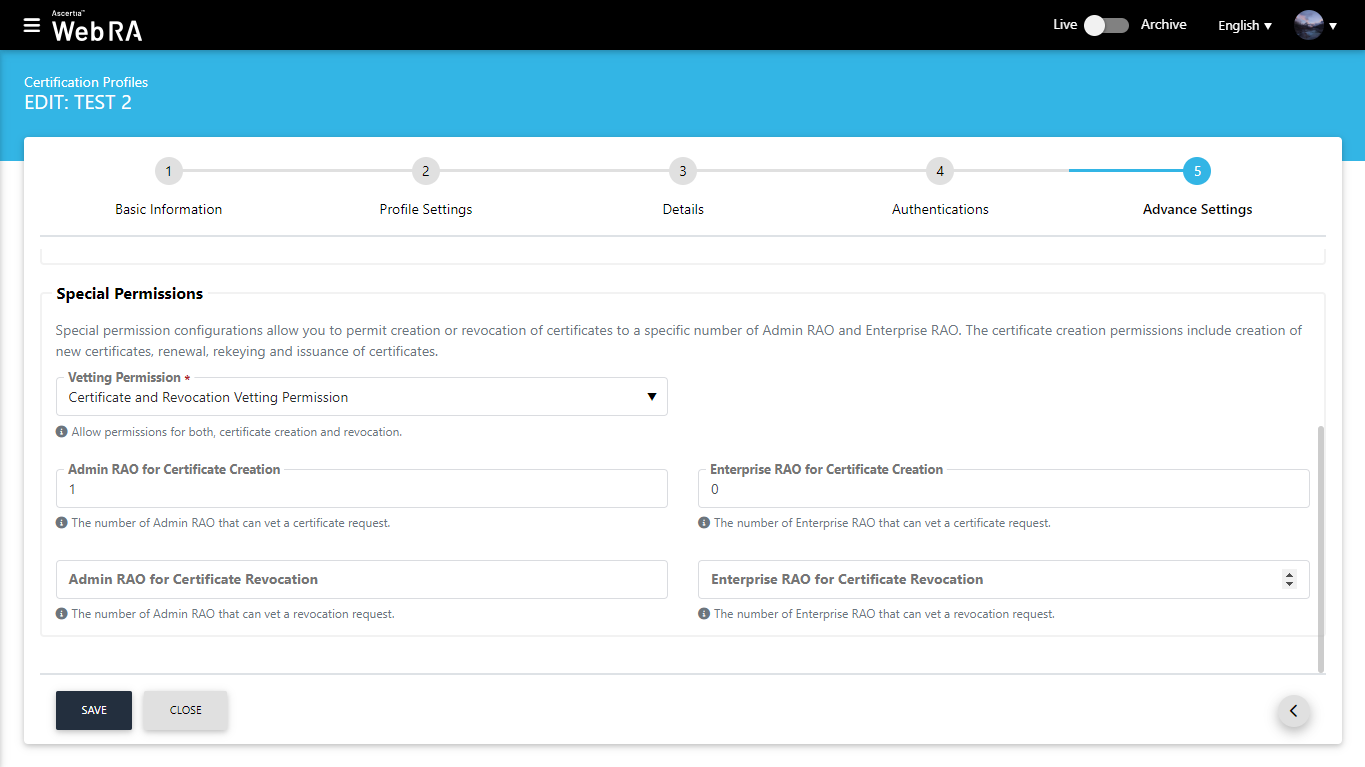
Special Permission |
Special permission configurations allow you to permit creation or revocation of certificates to a specific number of Admin RAO and Enterprise RAO |
|
Vetting Permission |
Vetting permissions for new certificate request.
|
|
Admin RAO for Certificate Creation |
The number of Admin RAO that can vet a certificate request |
|
Enterprise RAO for Certificate Creation |
The number of Enterprise RAO that can vet a certificate request |
Special Permission
ADSS Web RA allows an operator to configure/set number of Admin RAOs and Enterprise RAOs that will be required to approve requests for the following in the certification profiles:
- Creating a new certificate
- Renewal of certificate
- Certificate rekeying
- Certificate re issuance
|
|
It is important to note that this quorum will only be applicable when manual vetting is enabled. |
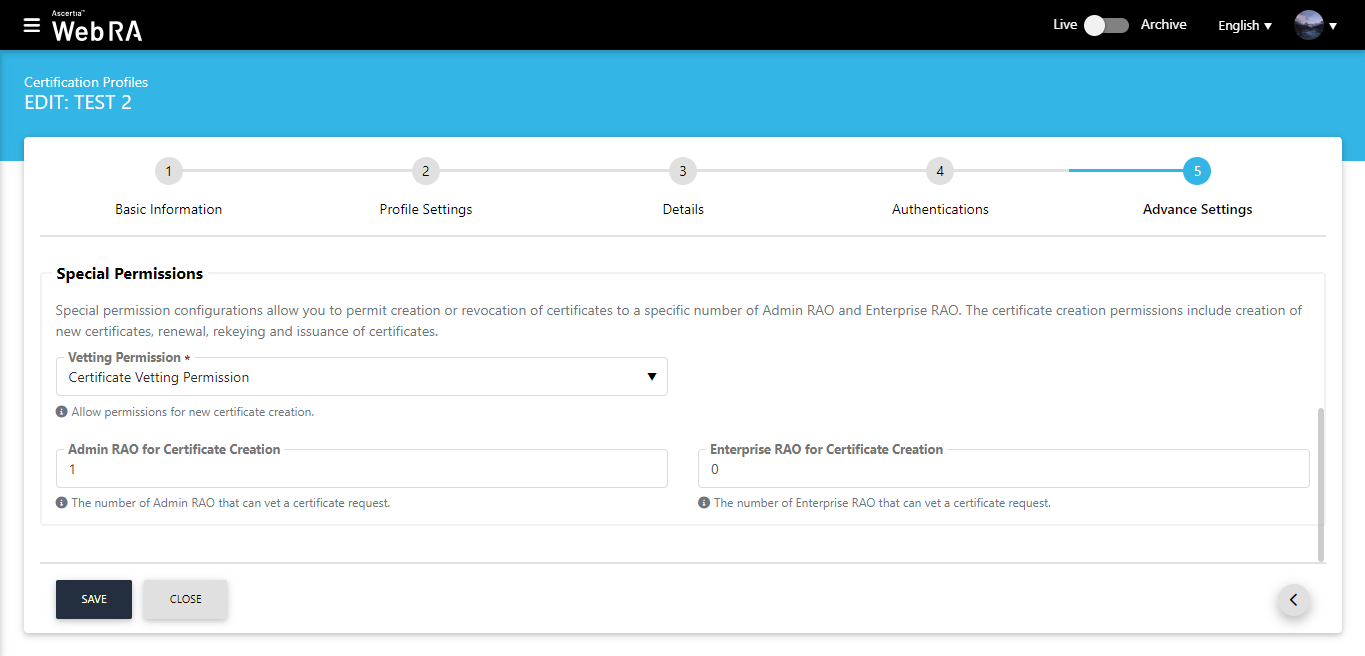
- An operator can set a limit on the number of the Admin RAO and Enterprise RAO that can perform various actions with respect to certification profiles (as mentioned above).
- An operator can permit either Admin RAO (s) or Enterprise RAO (s) or he can set permissions for both Admin RAO (s) and Enterprise RAO (s).
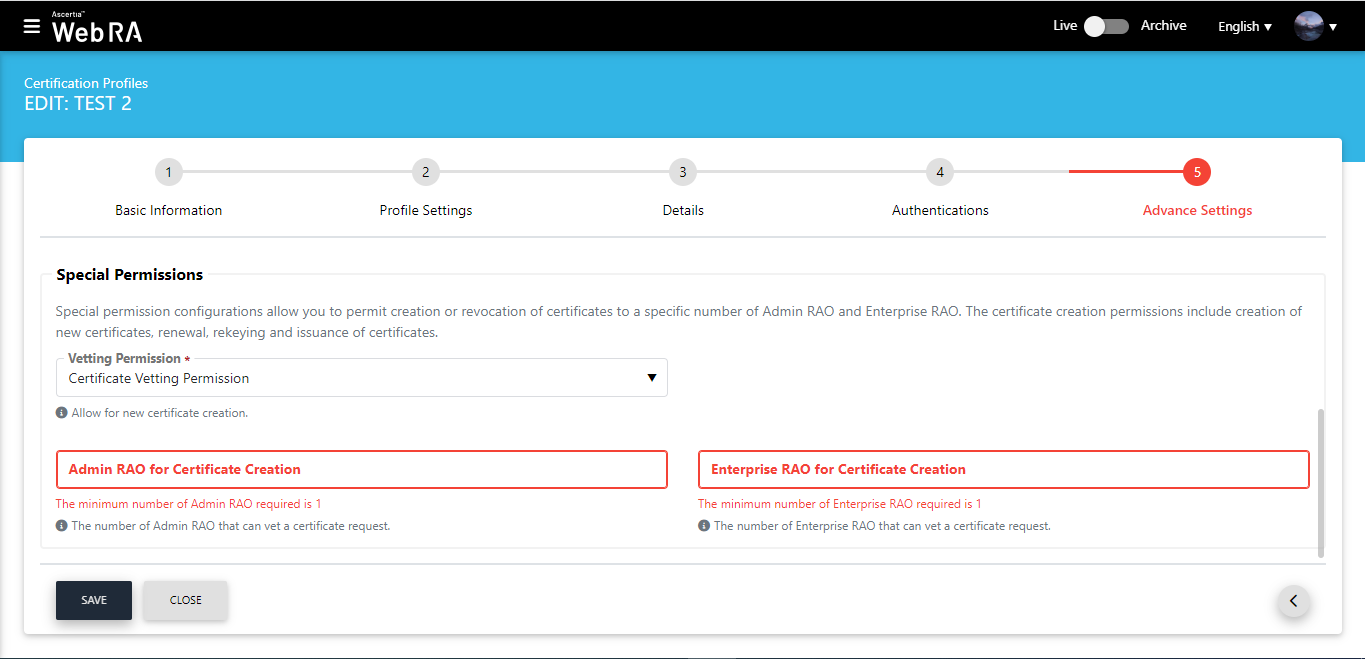
Minimum number of Admin RAO/Enterprise RAO required
An operator needs to permit at least one Admin RAO or Enterprise RAO. If an operator enters less than 1 Admin RAO/Enterprise RAO, the following messages will appear on the screen:
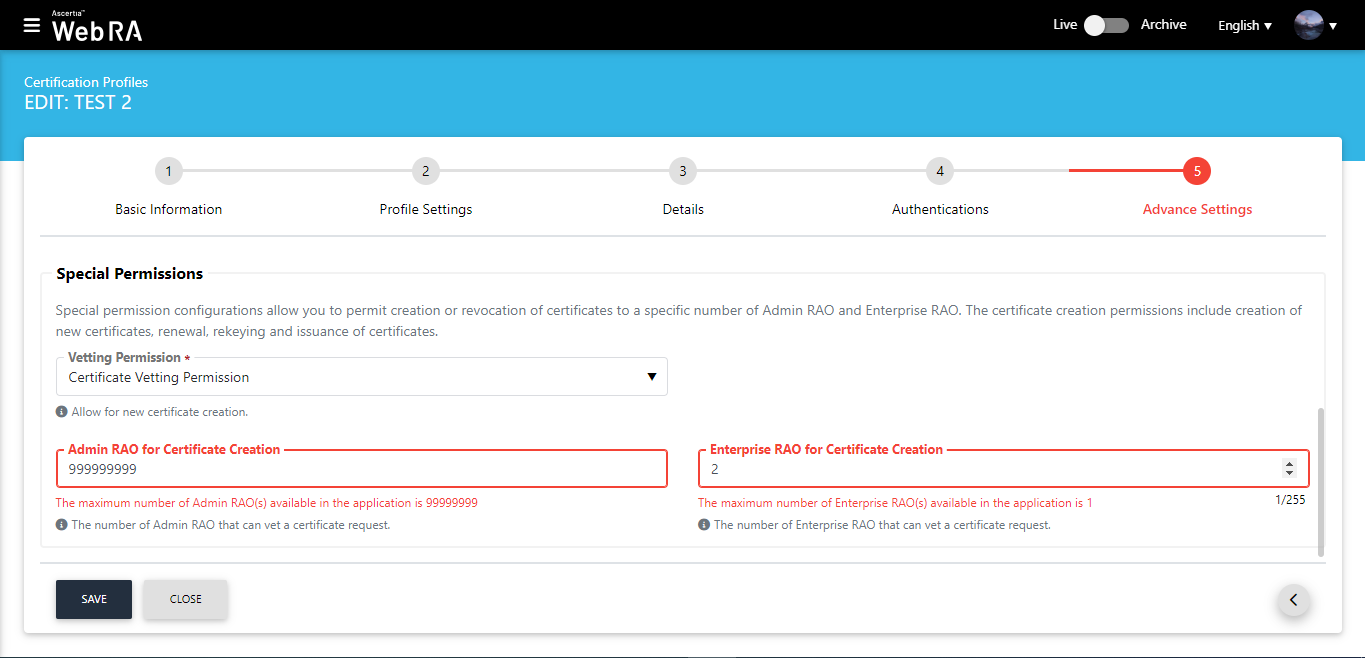
Maximum Limit on Number of Enterprise RAOs
If an operator enters a number more than the maximum number of Admin RAOs/Enterprise RAOs available in the application, the following messages will appear on the screen:
When an operator selects Certificate and Revocation Vetting Permission, the following screen appears:
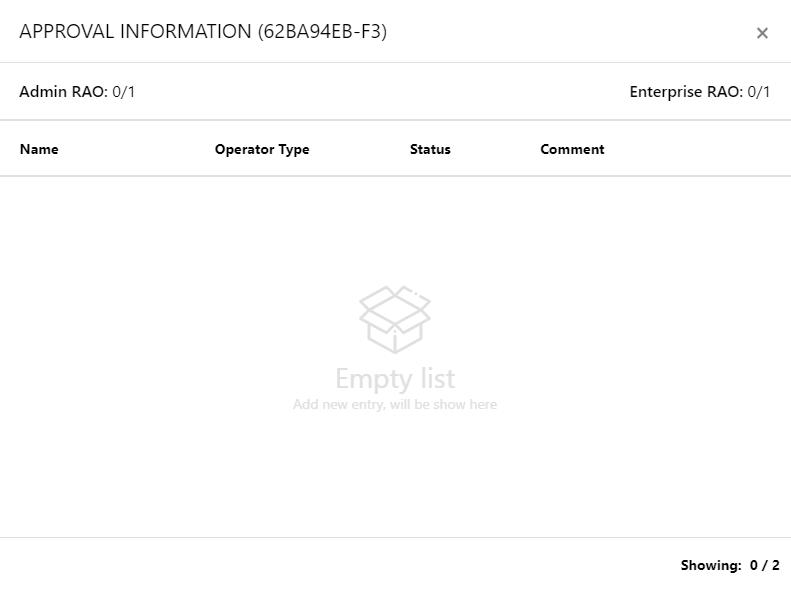
An operator can also view the number of approvers by clicking on the approver information link against a request.