Issued Certificates
Certificates issued by the Certification Service are shown here and certificates issued through Key Manager or Manual Certification (sub module of Manage CAs) are shown in the Manage CAs module. Those can be viewed within the Manage CA(s) service against the particular CA by clicking on the Issued Certificates button. If an end user certificate got renewed then it's old certificate will be marked revoked and a new certificate will be generated, in order to check the latest and revoked certificates for a particular end user, just expand the certificate by clicking on '+' button then all the old revoked certificates will be shown as child.
The Issued Certificates navigation button within the ADSS Certification Service allows you to view all certificates generated through the service interface: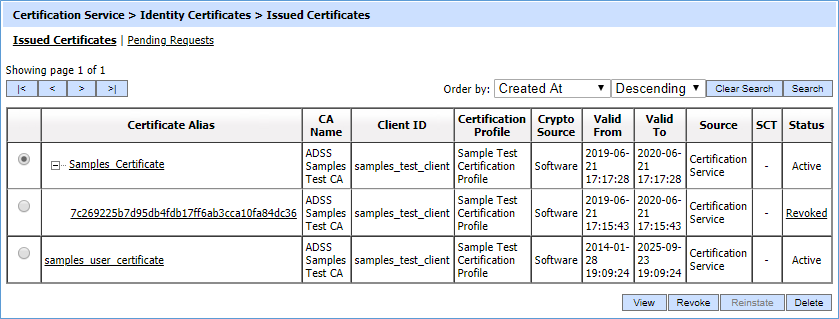
Each item in the screenshot is described below:
|
Items |
Description |
|
Certificate Alias |
A unique identifier for the certificate (as provided by the client application within the request message). |
|
CA Name |
The name (i.e. alias) of the CA that is issued the certificate. |
|
Client ID |
This is the Client ID as found in the request message. |
|
Certificate Profile |
The certification profile used to generate this certificate. |
|
Crypto Source |
Shows that this certificate is stored on software or hardware device. |
|
Valid From |
The “valid from” date of the certificate (taken from the certificate itself). |
|
Valid To |
The “valid to” date of the certificate (taken from the certificate itself). |
|
SCT |
CT column is shown only when certificate transparency module is enabled in license. By clicking the view link SCT request/response viewer is shown. |
|
Status |
Whether the certificate is labelled as “active”, “inactive” or “revoked” in the database. Note “inactive”and "revoked" certificates cannot be used for signing purpose, i.e. the ADSS Signing Service will not allow a revoked/inactive certificate to be used by a business application or user to sign a document. |
|
|
If an issued certificate is required to be deleted and the same certificate alias is required to be used for the new certificate then operator need to restart the ADSS Core, Console and Service instances from Windows NT Services panel or UNIX daemon. |
By clicking the view link SCT request/response viewer is shown: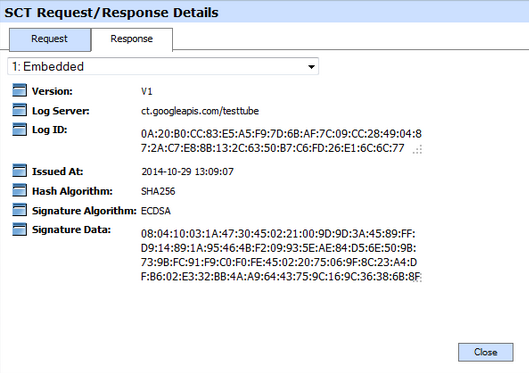
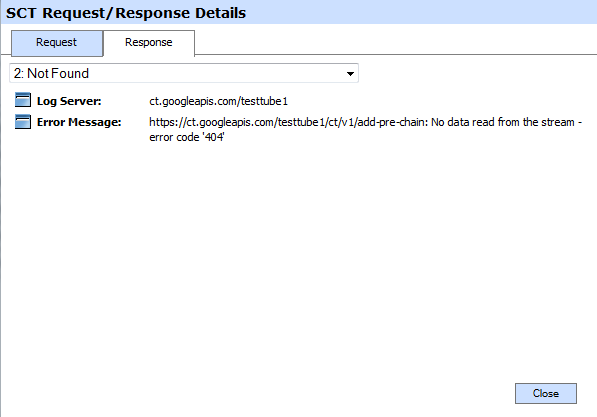
In case when SCT is not received from the Log Server then SCT Request/Response Viewer looks like:
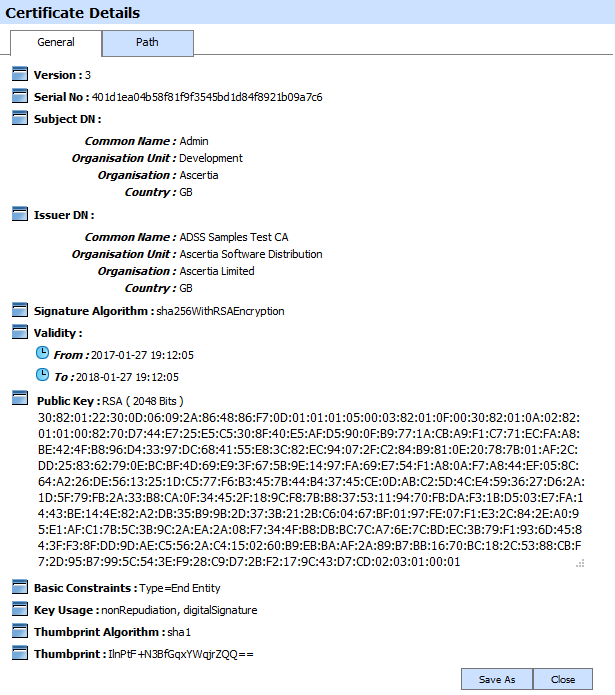
You can select a certificate, and then either View or Revoke or Delete it. By clicking on View and Certificate Alias, the issued certificate is shown like this:
|
|
The Organization Identifier will only be displayed in the Subject DN if the operator has enabled the 'Legal person semantic identifier' in Certificate Template while creating the required certificate. |
Clicking on the Revoke button will show the following screen where invalidity date, revocation code and hold instruction code can be provided before revoking the certificate:
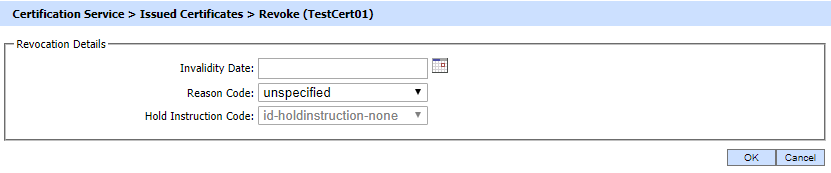
A certificate revoked with the certificateHold instruction code can be activated later on by using the Reinstate button. Once the certificate is revoked or activated, an instant revocation entry will be made into the database instead of issuing an emergency CRL for each revocation. CRL publishing is costly if they are published too frequently. To decrease the cost of resources, the idea of instant revocation is introduced. It works for the locally configured CA(s) only. External systems that are polling for CRLs issued by ADSS Server's Managed CAs have to download the CRLs in order the get the latest revocation information.
|
|
If a TLS Server or EV-TLS Server certificate is revoked using a non-keyCompromise reason code, the operator will be able to update the certificate again by clicking on the Revoke button. However, it should be noted that an already revoked certificate can only be updated with a keyCompromise reason code. The above mentioned functionality will only work if CA/B Forum is enabled in Global Setting > Advanced Settings. |
Clicking on the Revoke button for TLS Server or EV-TLS Server revoked certificate displays the following screen:
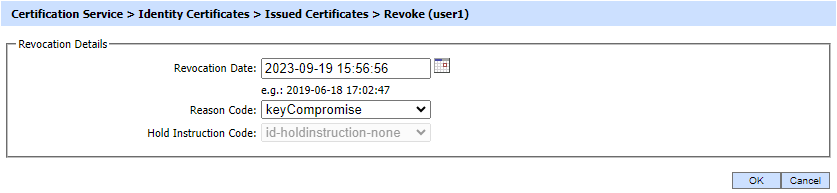
Here, the Invalidity Date field will be updated to Revocation Date and the Reason Code will be updated to keyCompromise. The operator will not be able change the Reason Code from the drop-down as a revoked certificate can only be updated with keyCompromise reason code.
The table below describes possible revocation reasons that can be selected:
|
Items |
Description |
|
unspecified |
This reason indicates that the certificate is revoked for an unknown reason. |
|
keyCompromise |
This reason indicates that it is known or suspected that the certificate subject's private key has been compromised. |
|
cACompromise |
This reason indicates that it is known or suspected that the certificate subject's private key has been compromised. |
|
affiliationChanged |
This reason indicates that the subject's name or other information has changed. |
|
superseded |
This reason indicates that the certificate has been superseded, a new certificate is replacing an existing certificate. |
|
cessationOfOperation |
This reason indicates that the certificate is no longer needed. |
|
certificateHold |
This reason indicates that the certificate has been put on hold (Revoke temporarily). One of the following hold instructions should be provided:
|
|
removeFromCRL |
This reason indicates that the certificate was previously on hold and should be removed from the CRL. |
|
privilegeWithdrawn |
This reason indicates that the privileges granted to the subject of the certificate have been withdrawn. |
|
aACompromise |
This reason indicates that it is known or suspected that the certificate subject's private key has been compromised. |
The list of issued certificates can be sorted in either Ascending or Descending order by selecting a table column from the drop down list.
|
|
While revoking a TLS Server or EV-TLS Server certificate from the ADSS Server, only the following reasons codes will be available to the operator in the Reason Code drop-down:
Note: The above mentioned functionality will only work if CA/B Forum is enabled in Global Setting > Advanced Settings. |
Clicking on the Search button on the Certification Service >> Issued Certificates main page will display the following screen:

This helps to locate a certificate that the Certification Service may have issued. Certificates can be searched based on issuer, certificate profile, certificate serial number, certificate subject DN, certificate alias, client ID, status, source, and validity period. If a search is based on multiple values, then these will be combined together using the “AND” operand, and thus only records that meet all the criteria will be presented.
|
|
If "_" character is used in the search then it will act as wildcard. |
See also

