Default OCSP Policy
If OCSP requests are not signed and there is at least one foreign (unregistered CA) CertID in the OCSP request then ADSS Server cannot apply the OCSP policy for the recognized CA. The Default Policy shown below is then used to process the unsigned OCSP request(s):
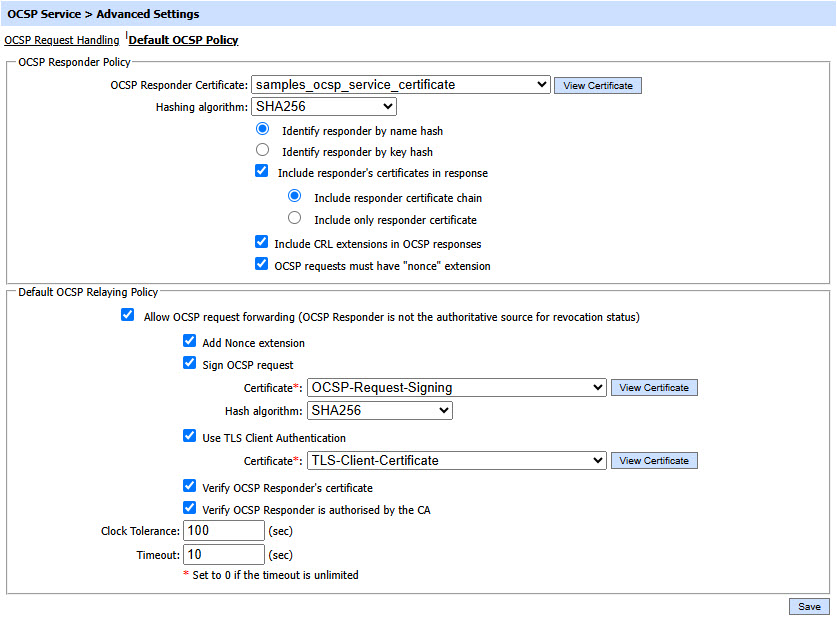
OCSP Responder Policy defines the following:
|
Items |
Description |
|
OCSP Responder Certificate |
Selected OCSP response signing certificate will be used to sign OCSP responses received from the peer responders. Note: When operating in FIPS 201 compliant mode, the ADSS Server operator must ensure that the length of the OCSP response signing key must be at least as large as, or larger than, the key length used by the CA that issued the target certificate (i.e. certificate being validated). |
|
Hashing Algorithm |
Selected hashing algorithm is used to sign the generated OCSP responses. The available options are SHA1, SHA-224, SHA256, SHA384, SHA512, SHA3-224, SHA3-256, SHA3-384, SHA3-512, RipeMD128 and RipeMD160. Note: When operating in FIPS 201 compliant mode, the ADSS Server operator must ensure that the hash algorithm configured for the OCSP response signing process must be at least as large as, or larger than, the hash algorithm used by the CA in issuing the target certificate (i.e. certificate being validated). Also note RipeMD128 and RipeMD160 are not available when operating in FIPS 201 compliant mode using a FIPS 140-2 evaluated hardware crypto module. |
|
Identify Responder By |
The OCSP Service can be configured to either include the responder name hash (i.e. common name of the OCSP response signing certificate) or the responder key hash. |
|
Include Responder's Certificates in response |
Select this option to include the intermediate certificate chain and/or OCSP response signing certificate within the generated OCSP response.
Note: If this option will be unchecked then neither response signing certificate nor response signing certificate chain will be included in the OCSP response. |
|
Include CRL extension in OCSP responses |
If CRL extensions and/or CRL references are available to the OCSP service then these will be included in the OCSP response message. The following CRL Entry Extensions are supported:
The following CRL references are supported:
|
|
OCSP requests must have "nonce" extension |
Determines whether or not the nonce extension should be present in the OCSP request messages that the ADSS OCSP service receives. If a nonce extension is required then any OCSP requests received without one causes a unauthorized error message to be sent back. |
Default OCSP Relying Policy defines the following:
|
Items |
Description |
|
Allow OCSP Request forwarding |
If selected then the OCSP service is allowed to relay the request to a peer OCSP Responder in case it is not authoritative for the target certificate. |
|
Add Nonce extension |
If this option is enabled then ADSS Server will add a nonce (i.e. a number used once) extension to the OCSP request message. The OCSP response is checked to ensure that it contains the same nonce value to prevent replay attacks. |
|
Add Service Locator extension |
If this option is enabled then ADSS Server will add the responder URL from the target certificate’s AIA extension into the OCSP request as a Service Locator extension. This helps the OCSP Responder to relay the OCSP request to other OCSP responders if the request cannot be handled directly. |
|
Sign OCSP Request |
Select this checkbox if the OCSP Responder requires OCSP request messages to be signed. Then select the OCSP Request signing Certificate which pre-exists in the Key Manager. |
|
Hash Algorithm |
Specify the hash algorithm to be used to generate OCSP request and furthermore to sign the OCSP request. |
|
Use TLS client Authentication |
If this option is enabled then OCSP service will communicate with peer OCSP responder using TLS client authentication. Select the Client TLS Certificate which pre-exists in the Key Manager. Note: It is required to register the Issuer CA of the Client TLS certificate in Trust Manager with the CA for verifying TLS client certificates purpose |
|
Verify OCSP Responder's certificate |
Select this checkbox if revocation checking of the OCSP Responder certificate is also required. Note: This is considered unusual since OCSP responder certificates are typically configured with a 'NOCHECK' extension. |
|
Verify OCSP Responder is authorised by the CA |
If this option is enabled then ADSS Server validates that the OCSP Responder that provides the OCSP response message is certified by the same CA that certified the target certificate; and furthermore that the OCSP Responder’s certificate was specifically marked by the CA for “OCSP Signing” in the certificates Extended Key Usage field. |
|
Clock Tolerance |
When verifying OCSP responses from peer responder, OCSP Service will compare the time within the OCSP response with its local clock to ensure they are “fresh” responses. System times may not be perfectly synchronized and so a tolerance value is essential. It is recommended that this is set to at least 100 seconds. |
|
Response timeout |
Defines how many seconds OCSP Service will wait for the peer OCSP Responder before assuming that there is a communication problem. It is recommended that this is set to at least 10 seconds. Note: Set to zero if the timeout is unlimited. |
See also
