Azure Key Vault
Azure is an Internet-scale computing and services platform hosted in data centres managed or supported by Microsoft. It includes many separate features with corresponding developer services which can be used individually or together. Azure Key Vault is one of the important services in Azure.
Azure Key Vault enables users to store and use cryptographic keys within the Windows Azure environment in both software and hardware formats. Azure Key Vault supports multiple key types and algorithms and enables the use of Hardware Security Modules (HSM) for high value customer keys. In addition, Azure Key Vault allows users to securely store Secrets in a Key Vault; Secrets are limited size octet objects and Azure Key Vault applies no specific semantics to these object. ADSS Server supports only Asymmetric Keys with Azure Key Vault. The below table shows the key sizes along with their respective hash algorithms which are supported in ADSS Server in case of Azure Key Vault:
|
Key Types / Curves |
Key Sizes |
Hash Algorithm |
Sign Algorithm |
|
ECDSA (NIST P) |
256 |
SHA256 |
SHA256WithECDSA |
|
384 |
SHA384 |
SHA384WithECDSA |
|
|
521 |
SHA512 |
SHA512WithECDSA |
|
|
RSA |
2048 |
SHA256 |
SHA256WithRSA |
|
3072 |
SHA384 |
SHA384WithRSA |
|
|
4096 |
SHA512 |
SHA512WithRSA |
|
|
|
|
RSASSA-PSS using SHA-256 and MGF1 with SHA-256 |
|
|
|
|
RSASSA-PSS using SHA-384 and MGF1 with SHA-384 |
|
|
|
|
RSASSA-PSS using SHA-512 and MGF1 with SHA-512 |
|
|
|
|
RawRSA |
If you are going to use ECDSA keys with Azure Key Vault crypto source, then we need to make sure that the Hash Algorithm are configured in accordance with their respective key size. For example, if we are using 256 key size for ECDSA keys, then it will be configured with SHA256 hash algorithm (as mentioned in the table above). Same methodology will be followed while using other key sizes for ECDSA keys.
|
|
There is no import/export key mechanism supported in ADSS Server from Azure Key Vault. |
|
|
Azure Key Vault does not support SHA3 Hashing Algorithm. |
A Key Vault may contain a mix of keys and secrets at the same time, and access control for the two types of object is independently controlled.
Users, subject to appropriate authorization, may:
- Manage cryptographic keys using Create and Delete operations.
- Use cryptographic keys with Sign/Verify operations.
Operations against Key Vaults are authenticated and authorized using Windows Azure Active Directory.
The Azure Key Vault Management system currently consists of two APIs, a REST API and a C# Client API. The REST API forms the base functionality for all programmatic interaction with the Azure Key Vault.
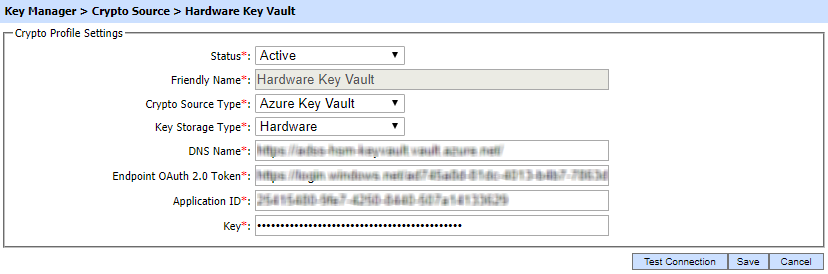
To generate a new Azure Key Vault profile press the New button in the Crypto Source Screen and select Azure Key Vault in Crypto Source Type drop down:
|
|
The Root CA of the URLs configured in DNS Name and Endpoint OAuth 2.0 Token must be registered in Trust Manager to establish the TLS connection otherwise the connection testing will be failed. Click here to learn how to export Root CA of the TLS Server Authentication certificate and add it in the Trust Manager. |
|
Items |
Description |
||
|
Status |
Set the status of this Crypto Profile. If the status is set to Inactive then it can not be used to generate or read the keys for singing purposes. |
||
|
Friendly Name |
Enter a friendly name for this Crypto device. The name should be unique within this ADSS Server environment. |
||
|
Crypto Source Type |
Select Azure Key Vault from the drop-down menu. |
||
|
Key Storage Type |
Select Hardware if you are suing the Premium Key Vault Service. Software for the Standard service. |
||
|
DNS Name |
It will be used to send requests to perform key operations like create key, delete key, sign etc. Received access token is passed in the request also. |
||
|
Endpoint OAuth 2.0 Token |
This URL will be used to authenticate the client from the Azure Active Directory. |
||
|
Application ID |
A Unique ID is assigned when an application is registered on the Azure Active Directory. |
||
|
Key |
A symmetric key hash when application is registered on the Azure Active Directory (acts as password).
|
For more details regarding configuration of Azure Key Vault with ADSS Server, refer to [ADSS-Server-Installation-Directory]/docs/Quick-Guide-for-Azure-Key-Vault-Configuration' document.
See also
Utimaco CryptoServer CP5 HSM
Thales Luna K7 Cryptographic Module
nCipher nShield Solo XC Cryptographic Module
AWS CloudHSM
MS-CAPI/CNG
Importing Existing Keys


