X.509 Certificates
The ADSS Manage CA(s) module supports the manual import and certification of RFC 2986 based PKCS#10 certificate signing requests (CSRs). The corresponding certificate is then issued against the imported PKCS#10 by one of the the configured Local CAs and External CAs.
To import a PKCS#10 and generate a certificate, click on the Manual Certification button and the following page will appear.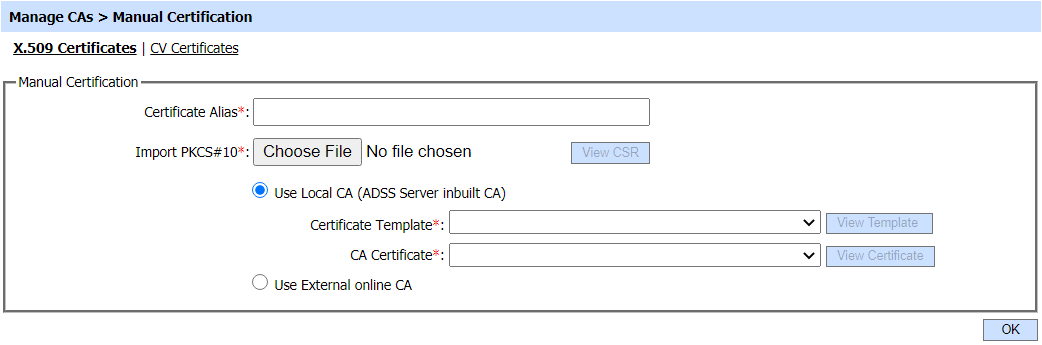
Name Constraints extension will be displayed if:
- 'Use Local CA' option is checked.
- Certificate template which has purpose 'Certificate/CRL Signing' is selected.
- Certificate template has Name Constraints extension enabled.
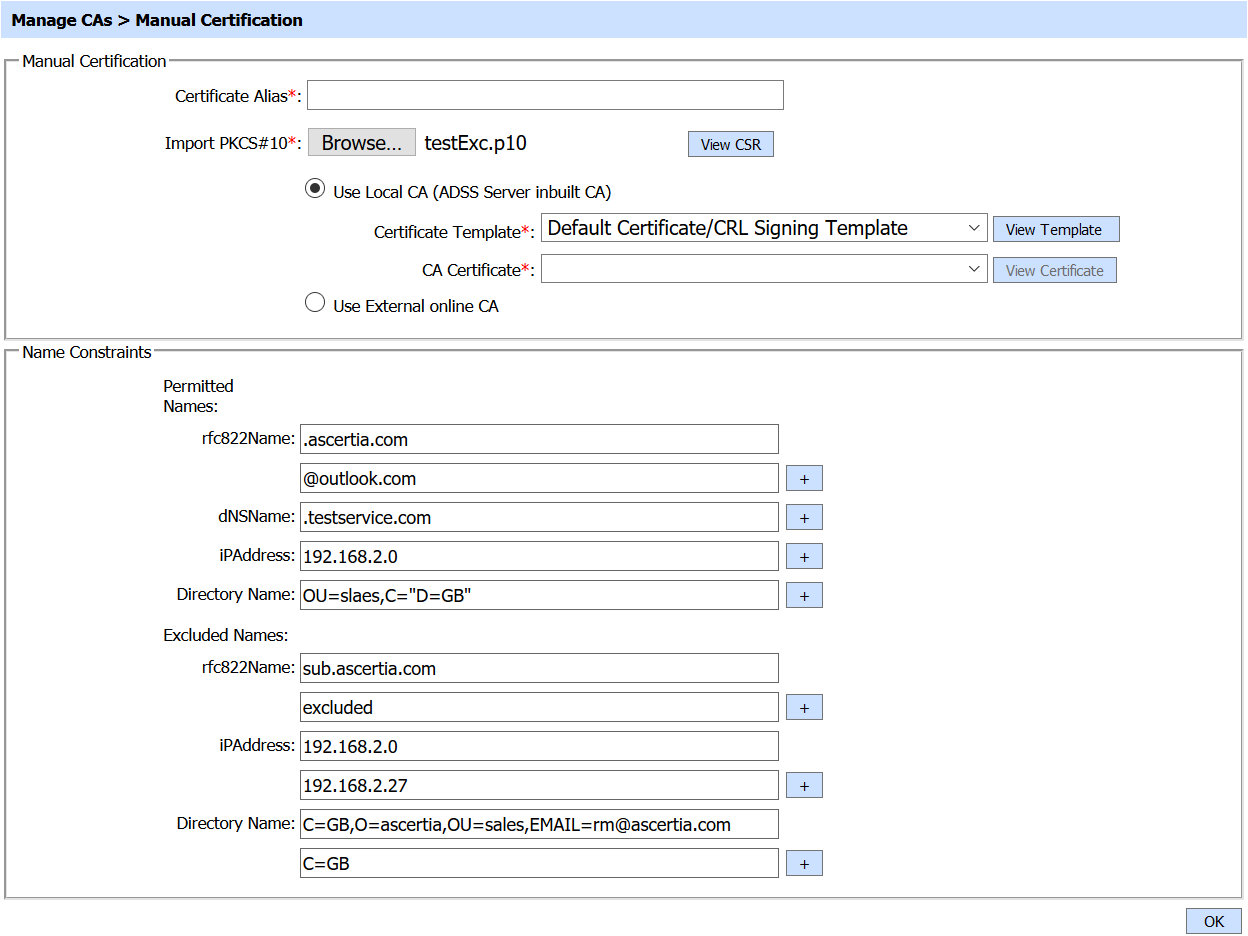
If PKCS#10 has name constraint extension, these name constraints will be displayed on the screen. The operator can manually change the values in the fields as well. Only those fields will be displayed that are enabled in certificate template.
Each element of the form is described below:
|
Items |
Description |
||
|
Certificate Alias |
Certificate Alias is the name of the certificate by which a certificate is recognized uniquely in ADSS Server.
|
||
|
Import PKCS#10 |
This is the path to the PKCS#10 on the file system. |
||
|
Use Local CA |
Select an internal CA that is configured to service the certification requests from the ADSS Certification Service. The ADSS Certification Service will send PKCS#10 certificate request messages to this internal CA. |
||
|
Certificate Template |
A certificate template defines the characteristics of the keys and certificates. |
||
|
CA Certificate |
This drop down shows the list of configured Local CA(s). Select one CA against which you want to issue the certificate. |
||
|
External CA |
Select this radio button to use an external online CA that is configured to service the certification requests from the ADSS Certification Service. The ADSS Certification Service will send PKCS#10 certificate request messages to this external CA. Currently the ADSS CA Server, Microsoft CA, GlobalSign EPKI and EJBCA are supported. |
||
|
Name Constraints |
Name Constraints section will only be visible if name constraints extension is enabled in the relevant certificate template having purpose 'Certificate/CRL Signing'. Name Constraints section will not be visible while generating self-signed certificates. This section contains following options: 1. rfc822Name
1. rfc822Name If [OU=excludedSutree1, O=TestCertificates 2011, C=US] is configured then following would not be allowed [CN=John, OU=excludedSutree1, O=TestCertificates 2011, C=US]. Multiple Directory Name can be added by clicking on '+' button. |
By clicking the OK button, the respective certificate (with or without name constraint extension) will be generated and you will be moved to the following page.
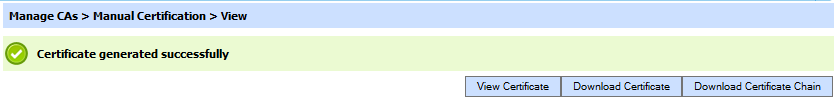
The generated certificate can be:
- Viewed by clicking on the View Certificate button.
- Downloaded by clicking on the Download Certificate button.
- Downloaded as part of a certificate chain (p7b) by clicking on the Download Certificate Chain button.
See also
