System Requirements
The following table lists the system requirements for ADSS Server:
|
Component |
Requirement |
|
ADSS Server |
ADSS Server is a Java 11 EE application supported on these platforms (ask about support for others):
Hardware:
About 1GB of database space is required to store the service logs from 100,000 transactions for each service unless these are regularly auto-archived or customised. |
|
Optional Database Server |
The database can be run on a separate server if preferred. This is recommended for high performance environments to allow all server resources to be directed to ADSS Server services. |
|
Client systems |
Any reasonable system. ADSS Client SDK for Java API requires JRE v1.7 or above. ADSS Client SDK for .NET requires Microsoft .NET Framework 4.5 or above. |
|
Operator Browsers |
The following browsers are supported for ADSS Server Operators:
|
|
Optional HSMs |
If required the following Hardware Security Modules are supported:
|
|
Optional DMZ proxy |
A DMZ proxy server can be configured if required. The following DMZ proxy machines are supported:
Use a reasonable CPU, 2GB RAM,100 MB disk space |
Typical Deployment Scenario
A typical ADSS Server installation schematic looks like this:
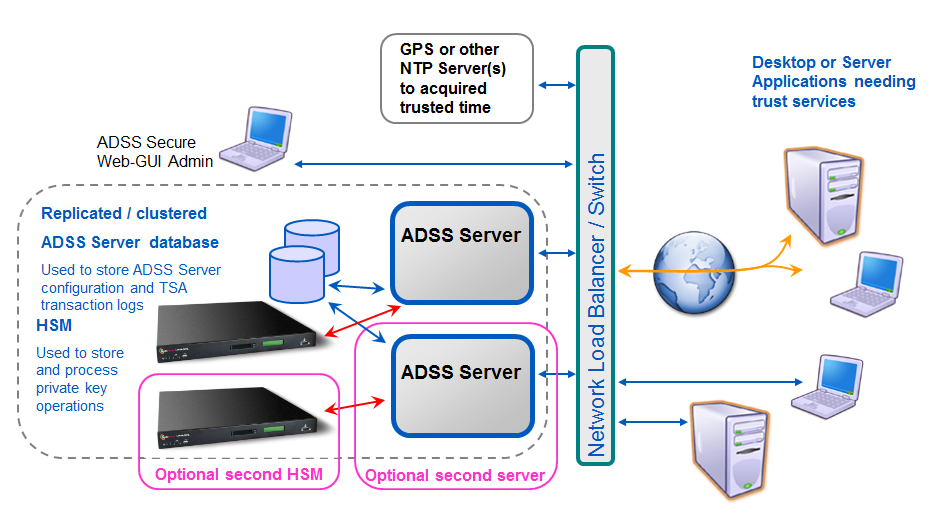
ADSS Server and the database it uses can both be installed on the same machine. 12GB RAM is recommended for such a scenario. For high performance environments, it is recommended to install them on separate systems.
The details shown above are the minimum system requirements; these may need to be revised to meet specific usage requirements. For high throughput systems consider using multiple load-balanced ADSS Servers in a network load-balanced resilient arrangement. Multiple physical CPUs can be added although additional licenses are required for these. Virtualized systems are also supported.
ADSS Server can also be installed on the same system as the business application it services.
HSM Support for Key Wrapping
If you wish to use ADSS Server with its HSM based user key generation wrapping and export under a static or dynamic KEK then be careful with the specifications of the HSMs you order or try to reuse.
The best thing to do is to run the ADSS Server PKCS#11 Test Utility to check if the HSM supports the mechanisms needed for this and indeed other functions. HSM vendors are known to change the mechanisms that are supported in this area, and some exclude such mechanisms from the allowable list when in FIPS 140-2. If in doubt check with Ascertia support and also check with your HSM vendor that the AES_CBC_ENCRYPT_DATA mechanism is supported for key wrapping and export.