SAML
A SAML based IdP can be configured as a connector in ADSS Server. The ADSS Server will redirect the user to this IdP for authentication. For example, this connector can be configured in ADSS RAS Service profile and during credentials authorisation, RAS Service will redirect the user to this SAML based IdP for authentication.
While configuring a SAML based IdP, the following screen will be displayed:
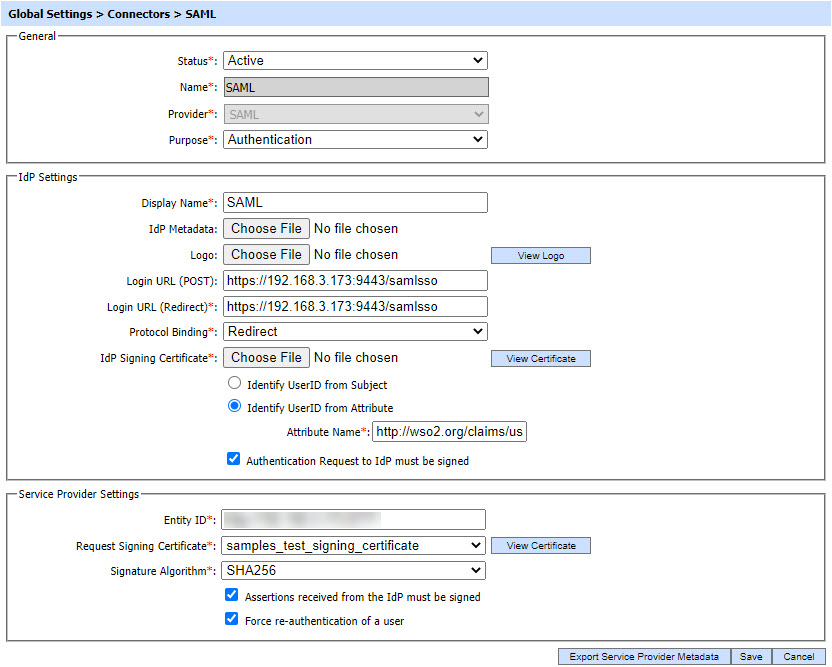
Clicking on Export Service Provider Metadata button will export the service provider metadata on the file system. This metadata file will contain the service provider configurations.
The configuration items are as follows:
|
Items |
Description |
|
Status |
This specifies the status of the Connector i.e. Active or Inactive. Only active connectors can be used within ADSS modules. |
|
Name |
A user friendly name assigned to each Connector for internal identification. |
|
Provider |
This drop-down field specifies the type of the Connector. Select SAML to configure a SAML based IdP as a connector. |
|
Purpose |
This specifies the purpose of Connector e.g. Authentication etc. |
|
IdP Settings |
This section defines configurations required to establish connection between IdP and ADSS Server. |
|
Display Name |
This field shows the name of the IdP that will be displayed to the user. |
|
IdP Metadata |
This field will be used to import the SAML IdP metadata file from the file system. The metadata file will contain all the configurations required to configure IdP in ADSS Server, hence if uploaded, the IdP setting fields below will be populated automatically. |
|
Logo |
This field is used to upload the logo image of external IdP from the file system that will be displayed to the user e.g. while authorising the credentials by RAS Service. The logo will be displayed along with the "Display Name" of IdP. Note: It's an optional field. It is recommended to use 32*32 or 48*48 pixels image resolution. |
|
Login URL (POST) |
This field shows the URL of IdP where ADSS will redirect the user for authentication using POST binding of SAML. Note: This URL will be used if POST binding is selected in Protocol Binding drop-down field. |
|
Login URL (Redirect) |
This field shows the URL of IdP where ADSS will redirect the user for authentication using Redirect binding of SAML. Note: This URL will be used if Redirect binding is selected in Protocol Binding drop-down field. |
|
Protocol Binding |
This field shows the binding type used by ADSS in order to communicate with external IdP. |
|
IdP Signing Certificate |
By using this field, an IdP Signing Certificate can be uploaded from the file system that will be used by ADSS to verify the signature computed by IdP on the SAML response or assertion. |
|
Identify UserID from Subject |
If this radio button is enabled, ADSS will get the user identifier from the Subject element of the SAML assertion. |
|
Identify UserID from Attribute |
If this radio button is enabled, ADSS will get the user identifier from the Attribute statement of the SAML assertion. |
|
Attribute Name |
This field will be available if Identify UserID from Attribute radio button is enabled. It allows the operator to set the attribute name to identify the user from assertion. |
|
Authentication request to IdP must be signed |
If this checkbox is enabled, a signed SAML request will be sent to the IdP by ADSS. |
|
Service Provider Settings |
This section defines configurations related to the Service Provider i.e. ADSS Server. |
|
Entity ID |
This field shows the identity of the service provider that will be sent to the IdP in each request. Note: Maximum characters allowed in this field are 1024. |
|
Request Signing Certificate |
This drop-down field will contain a list of certificates that can be used by ADSS in order to sign SAML requests. These certificates are generated in Key Manager module. Note: The drop-down will contain the certificates created using Document Signing purpose only. |
|
Signature Algorithm |
This drop-down will contain a list of digest algorithms that will be used to produce signature on SAML request. |
|
Assertions received from the IdP must be signed |
If this checkbox is enabled, ADSS insure that each assertion received in response from the IdP is signed. If the assertion is not signed, ADSS will reject the assertion. |
|
Force re-authentication of a user |
If this checkbox is enabled, ADSS will force the IdP to re-authenticate the user by sending a special flag in authentication request. The user will be forced to re-authenticate by IdP even if it has a valid session with the IdP. |
|
|
Currently SAML based IdP's can only be configured in RAS Profile of ADSS RAS Service. |
Clicking on Save button will save the applied configurations.
See also
